ISO 27001 Certification: 7 Steps to Get Certified
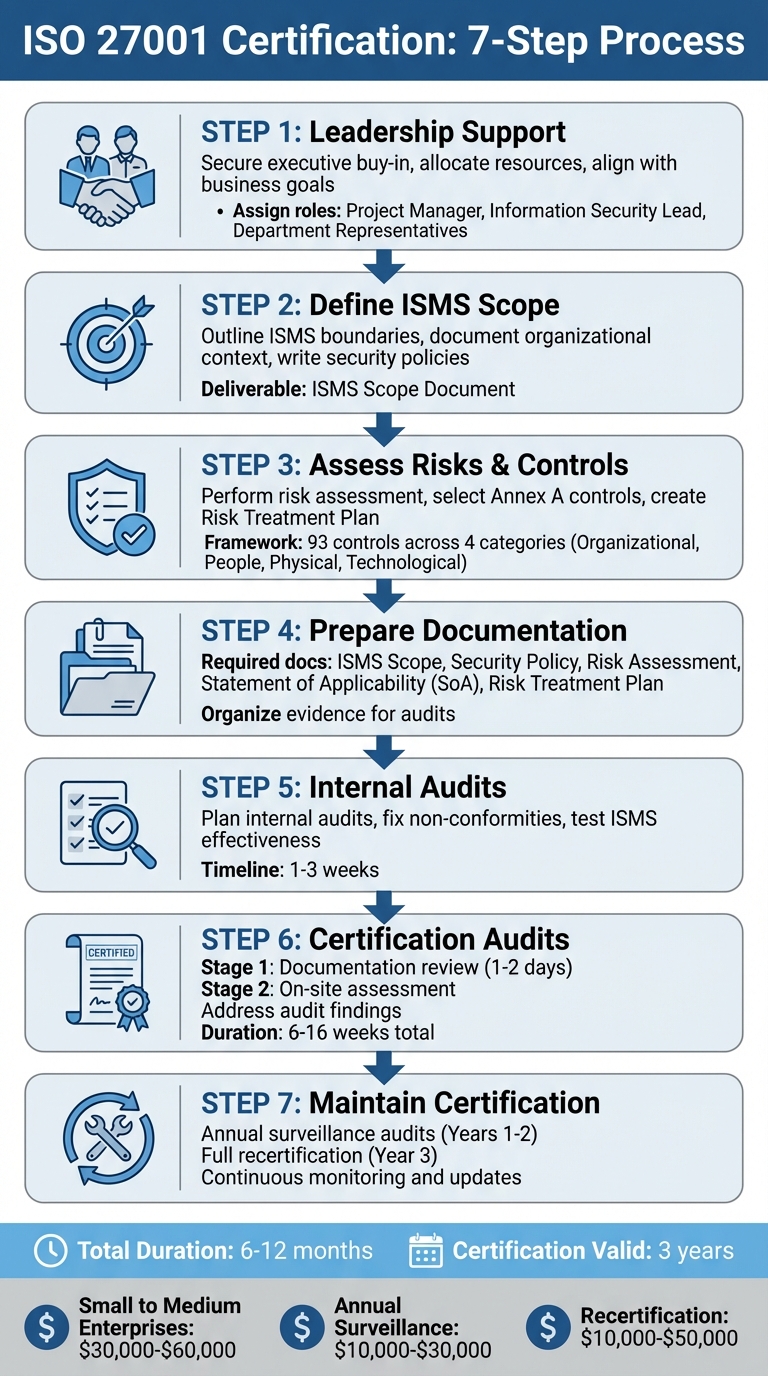
ISO 27001 certification is an internationally recognized standard for managing information security. It ensures your organization has a structured system to protect sensitive data, meet regulatory requirements, and reduce risks. The certification process involves seven key steps:
- Leadership Support: Secure executive buy-in, allocate resources, and align certification with business goals.
- Define ISMS Scope: Clearly outline the boundaries of your Information Security Management System (ISMS), including assets, departments, and systems.
- Assess Risks & Apply Controls: Identify risks, select appropriate Annex A controls, and create a Risk Treatment Plan (RTP).
- Prepare Documentation: Draft and organize required ISMS documents, including policies, risk assessments, and the Statement of Applicability (SoA).
- Internal Audits: Conduct audits to ensure compliance and address gaps before external certification.
- Certification Audits: Complete Stage 1 (documentation review) and Stage 2 (on-site assessment) with an accredited Certification Body.
- Maintain Certification: Pass annual surveillance audits, update your ISMS, and prepare for recertification every three years.
The process typically takes 6–12 months and costs $30,000–$60,000 for small to medium enterprises. Certification boosts credibility, reduces breach-related losses, and aligns with regulations like GDPR and HIPAA. Start by building a strong business case, conducting a gap analysis, and assembling a cross-functional team. With proper planning, ISO 27001 certification can be achieved efficiently.
ISO 27001 Certification Process: 7 Steps from Planning to Maintenance
Get ISO 27001 Certified in 12 Steps
sbb-itb-b92d866
Step 1: Get Leadership Support and Commitment
Achieving ISO 27001 certification hinges on active leadership involvement. Clause 5 of the standard emphasizes that executives must integrate the Information Security Management System (ISMS) into core business processes. They also need to provide clear evidence of resource allocation and policy approval during audits. Leadership plays a critical role in determining the timeline, budget, and overall alignment of the certification with broader business objectives.
Without executive sponsorship, these initiatives often face challenges in securing sufficient funding since they don't directly generate revenue. To gain leadership support, tie the certification to strategic goals, such as increasing sales, meeting GDPR or HIPAA requirements, and safeguarding critical assets.
Assign Leadership Roles
Start by forming a cross-functional team with clearly defined roles. Key positions include:
- Project Manager: Oversees the certification process, ensures milestones are met, and bridges communication between technical and non-technical stakeholders. This person should have project management expertise and a solid grasp of IT systems.
- Information Security Lead: Manages the technical aspects of ISMS implementation.
- Department Representatives: Include members from IT, operations, legal, and HR to ensure organization-wide involvement.
Many organizations also appoint a senior Management Representative - typically someone at the C-level or director level. This individual ensures ISMS effectiveness across departments and acts as a liaison between the implementation team and senior leadership. Document role assignments to demonstrate leadership involvement during audits.
With the team in place, the next step is to formalize management’s commitment to the certification process.
Secure Management Commitment
To get leadership fully on board, build a compelling business case that aligns with organizational priorities. Conduct a gap analysis to show where the organization currently stands and outline the steps needed to achieve certification.
Leadership must also establish a formal Information Security Policy. This policy should define specific security objectives and commit to ongoing improvements. Additionally, schedule regular management reviews - either quarterly or annually - to evaluate ISMS performance, audit outcomes, and risk management efforts.
Create Budgets and Timelines
Develop a detailed timeline with clear milestones for the certification process. This helps leadership understand the importance of allocating resources across departments and highlights potential challenges or delays. Your budget should cover:
- Certification body fees
- Internal staff time
- External consultants (if needed)
- Compliance software
- Technical upgrades like encryption tools or firewalls
| Phase | Key Activities | Estimated Timeframe |
|---|---|---|
| Phase 1: Planning | Leadership buy-in, scoping, ISMS setup, process definition | 1–4+ months |
| Phase 2: Audit | Auditor selection, evidence collection, internal audit, Stage 1 & 2 audits | 2–6 months |
| Phase 3: Maintenance | Control monitoring, annual surveillance audits | Ongoing (3-year cycle) |
Keep in mind, certification isn’t a one-time cost. Your budget should include annual surveillance audits and full recertification every three years. Build in extra time to address any non-conformities that may arise during audits.
Step 2: Define Your ISMS Scope and Context
After securing leadership buy-in, the next step is to clearly define the scope of your Information Security Management System (ISMS). According to ISO 27001 Clause 4.3, you’ll need to create a written ISMS Scope Document that outlines the physical, organizational, and technological boundaries of your system. This document sets the stage for your certification process by determining which assets, departments, and systems will be audited. It also directly affects the cost and timeline of certification.
It’s important to note that you don’t have to certify your entire organization. Many businesses opt to focus on specific areas like key departments, product lines, or locations that are critical to maintaining customer trust. While a narrower scope can reduce costs and speed up the process, it may leave certain parts of your organization outside the security framework. A broader scope, on the other hand, ensures more comprehensive coverage but requires a larger investment of resources.
Determine ISMS Scope
Start by identifying the assets and systems most essential to your organization. Think about the services, products, or platforms that play a significant role in building and maintaining customer trust. Your scope should include personnel, physical locations, and information systems that manage sensitive data.
Be sure to document any third-party interfaces or dependencies, such as cloud service providers or contractors, and explain any exclusions. Auditors will expect to see a rationale for these decisions, especially when it comes to managing risks tied to external relationships.
Your scope should align with your overall business strategy and take into account the requirements outlined in Clause 4.1 (internal and external issues) and Clause 4.2 (interested parties). For smaller organizations, the process of becoming audit-ready typically takes about four months. Once your scope is defined, document how internal and external factors influence your ISMS.
Document Organizational Context
To ensure your ISMS is effective, analyze the internal and external factors that could impact it. Internal factors might include your company’s governance structure, culture, available resources, and the locations where sensitive information is processed. Consider elements like company size, existing IT infrastructure, and policies for remote work.
External factors encompass the legal, regulatory, financial, and technological environment in which your organization operates. This includes compliance requirements like GDPR, HIPAA, or specific client security mandates. Additionally, identify your interested parties, such as customers, partners, regulators, and employees, and document their security expectations.
To support this analysis, maintain an asset register that lists hardware, software, and information assets, including details like name, type, location, and ownership. Conduct a gap analysis to compare your current security practices with ISO 27001 requirements. This will help you pinpoint areas that need attention. Use a risk matrix (e.g., a 1–5 scale) to rank the likelihood and impact of risks associated with specific factors.
| Factor Category | Examples to Document |
|---|---|
| Internal | Governance structure, staff resources, company culture, IT infrastructure |
| External | Compliance requirements (e.g., GDPR), emerging technologies, market competition |
| Stakeholders | Client requirements, shareholder expectations, regulatory obligations |
| Operational | Cloud dependencies, physical locations, remote work policies |
This detailed context analysis ensures that your ISMS aligns with both certification standards and your business goals.
Write Security Policies and Objectives
With your scope and context in place, it’s time to draft security policies that reflect your organization’s goals.
The Information Security Policy is a key document that demonstrates leadership’s commitment to the ISMS. This policy outlines the framework for proposing, approving, and reviewing security objectives across the company. It acts as the bridge between top management and security efforts, enabling executives to oversee ISMS performance without delving into technical details.
"The Information Security Policy should actually serve as a main link between your top management and your information security activities, especially because ISO 27001 requires the management to ensure that ISMS and its objectives are compatible with the strategic direction of the company." - Dejan Kosutic, CEO & Lead Expert, Advisera
To align the policy with leadership’s vision, interview your CEO and keep the document concise - avoid lengthy, unreadable policies. Define measurable security objectives that align with your risk assessment, and specify who will track progress and how often results will be reviewed. For larger organizations, it’s wise to separate the Information Security Policy from the Enterprise Risk Management Policy to maintain clarity.
Your security policies should directly address the risks identified during your assessment and adhere to ISO 27001 standards. Keep in mind that the 2022 update to ISO 27001 reorganized Annex A controls, reducing them from 114 to 93 and grouping them into four categories: Organizational (37 controls), People (8 controls), Physical (14 controls), and Technological (34 controls).
Step 3: Assess Risks and Implement Controls
With your ISMS scope in place, the next step involves evaluating risks and putting controls into action. This means identifying potential security threats, assessing their possible impact, and choosing suitable safeguards from the Annex A controls outlined in the standard. The decisions you make here will shape your security measures and demonstrate to auditors why these choices were made.
To ensure the process is consistent and repeatable, establish a clear methodology before diving in. Risk assessment isn't a one-and-done task - you'll revisit it as your organization grows, new threats arise, or your business environment shifts. The goal is to systematically identify and evaluate risks, forming the foundation of your risk management approach.
Perform Risk Assessment
Start by conducting a risk assessment based on your defined scope. Create a methodology - whether qualitative or numerical - to evaluate risks. Many organizations use a risk matrix with numerical scales (e.g., 1–5) to rate both likelihood and impact. Document this methodology upfront to ensure future assessments remain consistent and comparable.
Next, compile a detailed asset inventory. This should include hardware, software, data, and intangible assets like intellectual property or brand reputation. For each asset, pinpoint potential threats (like phishing attacks, natural disasters, or insider threats) and vulnerabilities (such as outdated systems, weak passwords, or lack of encryption). Document risks with specific scenarios for clarity.
"The standard doesn't prescribe a specific methodology - asset-based, scenario-based, or threat-led approaches are all valid. Choose what works for your organization and apply it consistently." - Saravanan G, Vice President - Cyber Assurance, Glocert
Assess each risk by scoring its likelihood (how often it might occur) and impact (the potential damage it could cause). Multiply these scores to determine a risk rating - higher scores signal higher-priority risks. Assign a risk owner to every identified risk; this person will oversee treatment plans and accept any residual risk.
Summarize your findings in a risk register. This document should detail each risk's score, assigned owner, and treatment plan. The risk register is key for audits and provides a clear view of your organization's risk landscape.
Select Annex A Controls
Once you've assessed your risks, it's time to decide how to address them. For each risk, select one of four treatment options:
- Modify the risk by implementing controls to reduce its likelihood or impact, like using Multi-Factor Authentication (MFA) to prevent unauthorized access.
- Retain the risk if it's within acceptable limits - this is typical for low-level risks where mitigation costs outweigh potential losses.
- Avoid the risk entirely by discontinuing the risky activity, such as retiring outdated software.
- Transfer the risk to a third party, for instance, through cyber insurance or outsourcing to a secure cloud provider.
After choosing a treatment option, map it to the relevant Annex A controls. The 2022 version of ISO 27001 includes 93 controls grouped into four categories: Organizational (37 controls), People (8 controls), Physical (14 controls), and Technological (34 controls). Select controls that directly address the risks you've identified.
"While the core risk assessment requirement for ISO 27001 didn't change with the update to the new 2022 version, it remains crucial to consider a wide range of risks to ensure that the controls your organization applies adequately address your identified security risks." - Ethan Heller, GRC Subject Matter Expert, Vanta
The 2022 update introduced 11 new controls targeting modern concerns like threat intelligence, cloud security, and data leakage prevention. It also requires organizations to evaluate whether climate change poses a risk to their ISMS, such as potential disruptions to data centers caused by extreme weather.
Document your control choices in a Risk Treatment Plan (RTP). This plan should outline the specific actions, assigned responsibilities, and timelines for implementing each control. Once finalized, these decisions are formalized in the Statement of Applicability (SoA).
Create the Statement of Applicability (SoA)
The SoA is a cornerstone document for audit preparation. It lists all 93 Annex A controls and indicates their relevance to your organization. During the Stage 1 audit, auditors will review this document to ensure your ISMS is well-designed.
For each control, the SoA must include the control reference number, title, applicability status (Yes or No), justification for the decision, and the current implementation status. Justifications are critical - auditors expect clear explanations for why controls are included or excluded based on your risk assessment.
Controls can only be excluded if they're genuinely irrelevant. For example, a fully remote company might exclude Control 7.4 (Physical security monitoring) with the justification: "100% remote organization; no physical premises". However, exclusions based on cost or priority won't pass audit scrutiny.
"Auditors can spot copy-paste risk assessments and weak SoA justifications instantly. Invest time in making these documents genuine, organization-specific, and defensible." - Saravanan G, Vice President - Cyber Assurance, Glocert
Your SoA should explicitly link each selected control to the risks it mitigates, proving that your security measures are rooted in a thorough assessment rather than guesswork. Compliance automation tools can simplify this process, with platforms like ISMS Copilot automating up to 80% of tasks, including evidence collection and risk mapping.
The SoA must evolve alongside your organization. Update it whenever your risk environment changes, such as adopting new technologies, entering new markets, or onboarding third-party vendors. Additionally, all organizations must transition to the ISO 27001:2022 framework by October 31, 2025. If you're certified under the 2013 version, this means updating your SoA to align with the new 93-control structure.
Step 4: Prepare ISMS Documentation
Once you've completed your risk assessment and chosen the necessary controls, the next step is documenting your Information Security Management System (ISMS). This documentation is crucial to demonstrate that your ISMS operates effectively and aligns with your organization's unique needs. Without it, even the best security practices won't meet the standards required for certification.
ISMS documentation serves two key purposes: it provides your team with clear guidance on implementing and maintaining security controls, and it gives auditors the evidence they need to confirm compliance with ISO 27001 requirements. Each document should establish a clear connection between your policies and practices, following a standard format that includes the policy's purpose, responsible department, approval and implementation dates, affected systems, and user acceptance tracking.
Required ISMS Documents
ISO 27001 outlines specific documentation requirements across Clauses 4 through 10. At a minimum, you’ll need to prepare:
- ISMS Scope (Clause 4.3): Defines the boundaries of your ISMS.
- Information Security Policy (Clause 5.2): Provides a high-level overview of your security approach.
- Risk Assessment and Treatment Methodologies (Clauses 6.1.2 and 6.1.3): Details your processes for identifying and addressing risks.
- Statement of Applicability (Clause 6.1.3): Lists selected Annex A controls and the rationale behind their selection.
- Security Objectives (Clause 6.2): Defines your organization's specific security goals.
In addition to these policy documents, operational records are essential to prove your ISMS is active and effective. Examples include:
- Risk Assessment and Treatment Results (Clauses 8.2 and 8.3): Evidence of how risks are managed.
- Training Records (Clause 7.2): Proof of employee competence.
- Monitoring and Measurement Results (Clause 9.1): Data showing how controls are performing.
- Internal Audit Programs and Results (Clause 9.2): Documentation of internal reviews.
- Management Review Outcomes (Clause 9.3): Evidence of leadership's evaluation of ISMS performance.
- Nonconformities and Corrective Actions (Clause 10.1): Records of issues identified and resolutions implemented.
You’ll also need to document any Annex A controls marked as applicable in your Statement of Applicability. Common examples include access control policies, asset inventories, incident response plans, and business continuity plans. Organize this documentation in a hierarchy, starting with high-level policies that explain the "what" and "why", followed by procedures and work instructions that detail the "how."
| ISO 27001 Clause | Required Document / Record | Purpose |
|---|---|---|
| Clause 4.3 | ISMS Scope | Defines the boundaries of the security system |
| Clause 5.2 | Information Security Policy | High-level overview of the security approach |
| Clause 6.1.2 | Risk Assessment Methodology | Defines the process for identifying and evaluating risks |
| Clause 6.1.3 | Statement of Applicability (SoA) | Lists selected Annex A controls and justifications |
| Clause 6.1.3 | Risk Treatment Plan (RTP) | Details actions, responsibilities, and timelines for risk mitigation |
| Clause 7.2 | Evidence of Competence | Training records proving employee qualifications |
| Clause 9.2 | Internal Audit Results | Records findings from the organization's self-assessment |
| Clause 9.3 | Management Review Results | Evidence of leadership's evaluation of ISMS performance |
| Clause 10.1 | Nonconformities and Corrective Actions | Documentation of issues found and how they were resolved |
Create Risk Treatment Plans (RTP)
The Risk Treatment Plan (RTP), required under Clause 6.1.3, outlines how your organization will address each identified risk. This document translates your risk treatment decisions into actionable steps. For each risk, you’ll choose one of four options:
- Modify: Apply controls to reduce the risk.
- Retain: Accept the risk as-is.
- Avoid: Stop the activity causing the risk.
- Transfer: Share the risk through insurance or outsourcing.
For example, if you decide to reduce the risk of unauthorized access by implementing multi-factor authentication (MFA), your RTP should specify which systems will use MFA, who will handle the configuration, and the deadline for implementation.
"The Risk Treatment Plan... defines when and by whom the controls will be implemented." - Advisera
Ensure your RTP aligns with the Statement of Applicability. Risk owners must approve the plan, including any residual risks, to confirm leadership’s agreement with the proposed actions. Use your risk matrix to prioritize the most critical issues, directing resources to the most pressing security gaps.
Organize Evidence for Audits
How you manage your documentation can significantly impact your audit experience. Auditors need to verify your ISMS design during the Stage 1 documentation review and confirm its implementation during the Stage 2 on-site assessment. Disorganized or outdated evidence can lead to delays and nonconformities.
Centralize all ISMS documents in a version-controlled repository, such as SharePoint, Confluence, or a compliance platform. This prevents confusion caused by conflicting document versions. Map each ISO 27001 requirement to specific evidence, such as access-review logs, encryption configurations, or signed training records. This checklist approach ensures nothing is overlooked before the external audit.
Maintain an up-to-date asset inventory, including details like owners, locations, and classifications. A reliable inventory supports your risk assessment and adds credibility. Similarly, keeping training records current demonstrates compliance with Clause 7.2.
Tools like ISMS Copilot can help automate compliance tasks by collecting technical evidence - such as access logs and configuration settings - directly from your systems. This saves time and allows your team to focus on refining policies and implementing controls.
Treat your internal audit as a "dry run" for the external audit. Have someone outside the ISMS management team review your documentation to identify gaps between written policies and actual practices. Address any issues and update your documents to reflect the current state of your ISMS. Rigorous version control is essential, as outdated risk assessments and asset inventories are common audit findings.
Once your documentation is solid, the next step is validating its effectiveness through internal audits.
Step 5: Run Internal Audits and Fix Gaps
Think of internal audits as your practice run before the big certification audit. According to ISO 27001 Clause 9.2, you’re required to conduct these audits at least once a year. Why? To spot and fix issues before an external auditor does. This is your chance to ensure your Information Security Management System (ISMS) isn’t just a well-documented plan but something that actually works in practice. Internal audits confirm that your processes are functioning as intended and effectively managing risks.
Here’s how internal audits differ from certification audits: internal audits focus on effectiveness - whether your controls are genuinely reducing security risks in your day-to-day operations. Certification audits, on the other hand, are all about conformity - proving that your ISMS aligns with ISO 27001 standards. A thorough internal audit helps you identify and address gaps in both areas before the certification process begins.
Plan Internal Audits
Start by defining the scope of your audit. Identify which IT systems, assets, and controls you’ll be assessing. Use your Statement of Applicability and risk assessment as your roadmap. Pay special attention to controls tied to high-risk areas highlighted in your risk assessment.
"The risk assessment can also provide insight into controls that internal auditors assess as part of a risk-based auditing approach. Specifically, auditors can assess controls mapped to risks with higher scores instead of assessing random control areas." - Marsel Fazilov, GRC Security Program Manager, Vanta
Choose an independent auditor - someone who hasn’t been directly involved in building or managing the parts of the ISMS they’ll be reviewing. While formal credentials aren’t mandatory, the auditor should have a solid understanding of ISO 27001 requirements and your organization’s security environment. If you don’t have the resources internally, hiring a third-party consultant can cost between $5,000 and $10,000 annually.
Prepare a checklist that covers all the required documentation (like ISMS scope, policies, and risk assessments) as well as operational records (such as training logs, incident reports, and monitoring results). Most internal audits are completed within one to three weeks.
During the audit, conduct interviews, observe processes, and test controls. For instance, you might verify that access reviews are happening on schedule by checking logs or confirm that employees have completed security training by reviewing a sample of training records. Mock interviews can also help staff get comfortable with auditor questions and reveal any weak spots in your processes.
Fix Non-Conformities
Document all findings from the audit and classify them into three categories:
- Major Nonconformities: System-wide failures, like missing risk assessments.
- Minor Nonconformities: Isolated issues, such as an incomplete training record for one employee.
- Opportunities for Improvement: Areas that meet requirements but could perform better.
Major nonconformities need to be resolved within 30 to 60 days and require follow-up verification before you can proceed with certification. Minor nonconformities usually allow for 30 to 90 days for correction. For each issue, perform a root cause analysis (using methods like the "5 Whys") to figure out why the problem occurred, not just what went wrong. Address both the immediate issue (correction) and the underlying process (corrective action) to prevent it from happening again.
Present the findings to senior management to secure the resources needed for remediation. To maintain objectivity, the person addressing the issue should not be the same person who identified it. Once changes are implemented, verify that they’ve resolved the issue before marking the nonconformity as closed. Even minor incidents and near misses should be recorded to show continuous improvement in your ISMS.
Test ISMS Effectiveness
Internal audits are more than just a compliance exercise - they’re about proving that your controls work in real-world scenarios. Check everything from encryption settings and access permissions to incident response processes and control performance using monitoring data. Ensure your asset inventory is always up to date.
Treat the internal audit as a final quality check. Have someone outside the ISMS management team review your documentation to catch any discrepancies between what’s written and what’s actually being done. A well-executed internal audit not only ensures compliance but also confirms that your ISMS is effective, minimizing the chances of surprises during the external certification audit.
Step 6: Complete Certification Audits
Once your internal audits confirm that your Information Security Management System (ISMS) meets the necessary requirements, it’s time to move on to the external certification audit. This step validates that your ISMS is not only structured correctly but also functioning as intended. The process involves two stages, each focusing on a different aspect of your system. Stage 1 reviews your documentation to ensure your framework is in place and logical. Stage 2 checks whether your organization is following its documented processes. The entire journey from Stage 1 to receiving your certification typically takes between 6 and 16 weeks.
These audits are carried out by an accredited Certification Body (CB). It's crucial to ensure your chosen CB is accredited by a recognized authority such as ANAB, UKAS, or IAS. The total cost for both stages generally ranges from $10,000 to $50,000, depending on the size and complexity of your organization.
Stage 1: Documentation Review
At this stage, your ISMS documentation undergoes a thorough review. Often referred to as the readiness review, this step ensures your documentation is complete and aligns with ISO 27001 standards. Typically lasting 1–2 days, the audit can be conducted on-site, remotely, or through a hybrid approach.
"Think of Stage 1 as 'Do you have what you need?' and Stage 2 as 'Are you doing what you say?' Stage 1 checks your blueprints; Stage 2 verifies the building is constructed to specification." - Saravanan G, Vice President - Cyber Assurance, Glocert
Auditors will assess key documents such as your ISMS scope statement, information security policies, risk assessments, risk treatment plans, Statement of Applicability (SoA), security objectives, internal audit records, and management review minutes. The goal here is to confirm that your framework exists and makes sense for your organization, not yet to evaluate its implementation. Common pitfalls include incomplete risk assessments, missing SoA documentation, lack of evidence for internal audits, and absent management review records.
The outcome of this stage is a readiness report. Based on their findings, auditors may recommend moving to Stage 2, proceeding with observations, or delaying Stage 2 if significant gaps are identified. If they issue "Improvement Requests", you’ll have about 6–8 weeks to address these before Stage 2. To streamline the process, organize all documentation in a clearly labeled and versioned folder so auditors can easily access what they need.
Stage 2: On-Site Certification Audit
Stage 2 focuses on verifying that your ISMS is operational and effective. This part of the audit is usually conducted on-site, with the duration depending on the size and complexity of your organization.
"If you said you should do something in your documentation, or Statement of Applicability, you'll need to prove you've done it." - Alan Parker, ISO 27001 Consultant, Iseo Blue
Auditors will interview staff at various levels to assess their understanding of security policies and observe processes in action. They’ll also review technical evidence such as access logs, incident reports, training records, and monitoring data. For example, they might check if scheduled access reviews are being conducted by examining logs or confirm that employees have completed security training by reviewing certificates.
To prepare your team for these interviews, conduct role-specific briefings so employees can confidently explain their security responsibilities. Auditors often use these discussions to determine whether your ISMS is integrated into daily operations or merely exists on paper. The final recommendation from the auditor will decide if your organization receives certification. Any findings identified during this stage will need to be addressed.
Address Audit Findings
Audit findings are categorized into three types: Major Nonconformities (system-wide failures or missing required elements), Minor Nonconformities (isolated issues that don’t indicate systemic problems), and Observations or Suggestions for Improvement (non-mandatory recommendations).
Major nonconformities must be resolved and verified before certification is granted, typically within 30 to 90 days. Minor nonconformities allow certification to proceed once a corrective action plan is approved, with follow-up verification during the next surveillance audit. For each issue, conduct a root cause analysis to understand why it happened, not just what went wrong.
The corrective action process involves several steps: acknowledging the finding, analyzing the root cause, implementing immediate corrections, establishing long-term corrective actions, gathering evidence of these actions, and submitting the evidence to the Certification Body for verification. Major nonconformities may require a follow-up on-site visit. Be meticulous in documenting everything - logs, updated procedures, training records - as proof that the issues have been addressed. Once all major nonconformities are resolved and minor issues have approved corrective action plans, you’ll receive your ISO 27001 certificate, which remains valid for three years.
Step 7: Maintain Certification and Improve Continuously
Achieving ISO 27001 certification is just the beginning. The real challenge lies in maintaining compliance and continuously improving your Information Security Management System (ISMS). While the certification is valid for three years, staying certified requires annual surveillance audits, regular internal evaluations, and ongoing enhancements to your ISMS framework.
Prepare for Surveillance Audits
Surveillance audits take place annually during the first two years of your certification cycle. These audits ensure that your ISMS remains effective and aligned with ISO 27001 standards. Unlike the initial certification process, the scope of these audits is narrower. They typically cover all ISO 27001 clauses, with Annex A requirements divided across the two years. The cost for these audits generally ranges from $10,000 to $30,000 per year.
Auditors will revisit any nonconformities identified during your initial certification or previous surveillance audits to confirm they’ve been resolved. Additionally, they’ll check that you’ve conducted mandatory internal audits at least once every 12 months, as required by Clause 9.2. To ensure you’re prepared, schedule internal audits about six months before your next surveillance audit. This gives you ample time to identify and address any gaps.
Key practices to stay audit-ready include:
- Conducting quarterly access reviews
- Running regular vulnerability scans
- Testing incident response procedures
Document even minor security issues or "near misses" to show that your ISMS supports continuous improvement. Store all audit logs, training records, and risk assessments in a centralized system. Relying on scattered tools like email or spreadsheets can lead to misplaced data and longer audits. These steps will make the transition to recertification much smoother.
Plan for Recertification
After two years of surveillance audits, prepare for the full recertification audit in the third year. This process is similar in scope to the initial Stage 2 certification audit and evaluates your entire ISMS, including all clauses and applicable Annex A controls. Successfully completing this audit renews your certification for another three years. The cost of recertification audits typically ranges from $10,000 to $50,000, depending on your organization’s size and complexity.
Start preparing at least six months in advance. Update all ISMS documentation, such as risk assessments, the Statement of Applicability, and security policies. Ensure management reviews reflect active leadership involvement, and conduct an internal audit that mirrors the recertification scope. These proactive steps will help you meet the rigorous requirements of the recertification process.
Monitor and Update Your ISMS
Your ISMS should adapt as your organization evolves and as new threats emerge. Update risk assessments annually or whenever significant changes occur, such as vendor integrations, product launches, or infrastructure upgrades. Senior leadership should review the ISMS annually - though biannual reviews are even better - to assess performance, audit findings, and necessary adjustments.
Regular staff training is another crucial element. Conduct training sessions twice a year to reinforce shared security responsibilities. When offboarding employees, immediately revoke their system access, update shared passwords, and retrieve company devices. Additionally, perform annual vendor security reviews to update risk scores and agreements in line with your current IT environment.
To measure your ISMS’s effectiveness, track key performance indicators (KPIs) like the percentage of critical patches applied or the frequency of failed login attempts. These metrics provide tangible proof of your system’s ongoing performance and compliance.
Conclusion and Next Steps
Getting ISO 27001 certification isn’t something you can wing - it requires a well-organized plan. On average, the process takes anywhere from 6 to 12 months, and once achieved, the certification is valid for three years.
Key Takeaways
Here’s what you need to know to make the process smoother:
- Leadership is crucial: Without executive support to allocate budgets, approve policies, and set the tone for a security-focused culture, the entire effort can stall.
- Focus on risks: A risk-based approach helps you pinpoint threats unique to your organization and decide which of the 93 Annex A controls to put in place.
- Document everything: Clear records - like the ISMS scope, risk treatment plans, and evidence of effective controls - are essential for auditors.
- Two-stage audit process: First, auditors review your documentation. Then, they assess how well your controls work in practice. Both steps are critical for certification.
- Consistency matters: Strong compliance depends on repeatable, evidence-based processes such as risk assessments, monitoring, and ongoing improvements.
Simplifying Certification with Technology
Manually managing compliance through spreadsheets and scattered files? That’s a recipe for wasted time and mistakes. ISMS Copilot offers a smarter way. This AI-powered platform automates tasks like collecting evidence, creating risk treatment plans, and organizing documentation - all in one place. It even integrates with your existing tools to automatically gather proof that your controls are working. By automating up to 80% of the work and offering real-time monitoring, ISMS Copilot turns compliance from a one-time project into a continuous process.
Start Your Certification Journey
Now it’s time to put these insights into action. Start by securing executive buy-in and aligning the certification effort with strategic goals, such as improving sales cycles, meeting regulatory requirements, or protecting key assets. Assemble a cross-functional team - including members from IT, HR, Legal, and Operations - and appoint a project manager to keep everything on track.
When defining the ISMS scope, smaller organizations might find it easier to focus on a specific product line or data environment. This approach can help streamline the process and manage costs effectively.
Next, conduct a gap analysis to see how your current security measures stack up against ISO 27001 standards. From there, tools like ISMS Copilot can help you automate tasks like documentation, risk assessments, and policy management.
"Scoping an ISMS can be challenging for organizations of all sizes. The trick is crafting a Scope Statement for your ISO 27001 certification that provides value for your customers and includes relevant systems and processes within the scope."
- Tim Blair, Sr. Manager and GRC Subject Matter Expert, Vanta
With the right preparation and tools, achieving certification within 6 to 12 months is entirely possible, setting the stage for a strong, security-first culture.
FAQs
How long does it take to get ISO 27001 certified?
The journey to achieving ISO 27001 certification usually takes anywhere from 3 to 12 months, but the exact timeline can vary based on a few key factors. These include how prepared your organization already is, the resources you can allocate to the process, and how complex your Information Security Management System (ISMS) is.
For smaller organizations or those with strong security measures already in place, the process might move along more quickly. On the other hand, larger companies or those starting from scratch may need additional time to get everything in order. Careful planning and leveraging tools like ISMS Copilot can make the process smoother and help keep things on track.
What are the key expenses involved in getting ISO 27001 certified?
The costs associated with obtaining ISO 27001 certification generally fall into three main categories:
- Preparation Costs: These include expenses for training, conducting a gap analysis, and acquiring any tools or resources needed to evaluate your current security posture and get ready for compliance.
- Implementation Costs: This involves the development and rollout of an Information Security Management System (ISMS). You might need to hire consultants, invest in software, or allocate internal resources to meet the standard's requirements.
- Certification Audit Costs: This is the fee paid to an accredited certification body for conducting the formal audit and issuing your ISO 27001 certificate.
The total cost depends on factors like your organization's size, complexity, and how prepared you are. With thoughtful planning, you can manage these expenses effectively.
How can our organization maintain ISO 27001 compliance after certification?
To keep up with ISO 27001 compliance, organizations need to prioritize consistent monitoring, routine audits, and ongoing enhancements to their Information Security Management System (ISMS). Regular internal audits are crucial to verify that controls are effective and continue to meet the standard's requirements. Additionally, management reviews play a key role in assessing the ISMS's performance and spotting areas that could use improvement.
It’s also important to stay ahead of the curve by updating policies and controls to address emerging risks or advancements in technology. Annual surveillance or recertification audits are essential for showing your commitment to ISO 27001 standards. Building a workplace culture that values security awareness and weaving risk management into everyday activities are just as critical. Tools like ISMS Copilot can simplify the compliance process and help your organization stay aligned with the standard.
Incorporating these practices into daily operations not only helps maintain certification but also strengthens your overall approach to information security over time.

