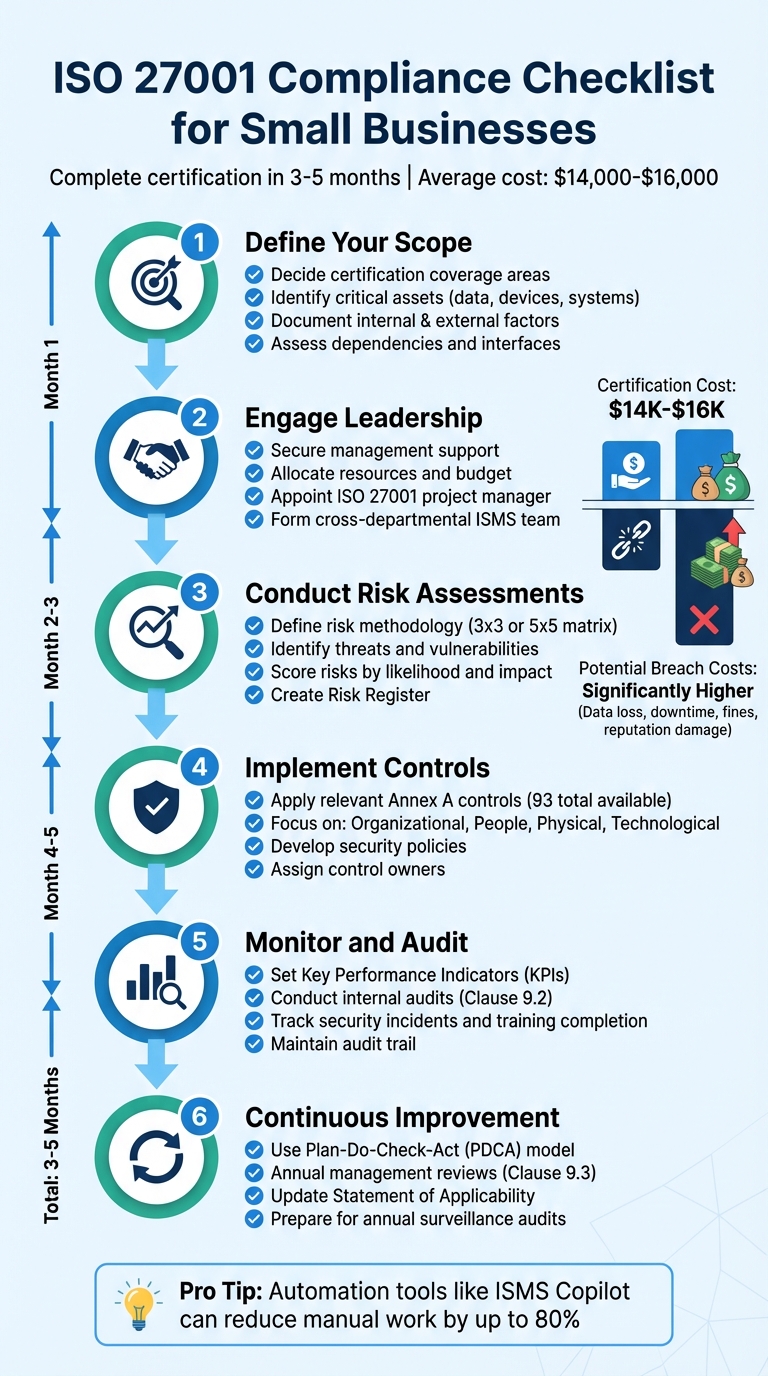
ISO 27001 Compliance Checklist for Small Businesses
ISO 27001 is the global standard for securing information. For small businesses, it’s not just about protection - it’s about building trust, meeting client demands, and avoiding costly breaches. Here’s a quick breakdown to get started:
- Define Your Scope: Decide what parts of your business the certification will cover.
- Identify Critical Assets: List and prioritize sensitive data, devices, and systems.
- Engage Leadership: Secure management support and allocate resources.
- Conduct Risk Assessments: Identify risks, evaluate them, and decide how to address them.
- Implement Controls: Use ISO 27001’s Annex A to apply relevant security measures.
- Monitor and Improve: Continuously track performance, conduct audits, and refine processes.
Small businesses typically spend $14,000–$16,000 on certification, which can be completed in 3–5 months. Automating tasks with tools like ISMS Copilot can reduce manual work by up to 80%, making compliance more manageable. Certification not only safeguards your business but also opens doors to new partnerships and opportunities.
ISO 27001 Compliance: 6-Step Implementation Process for Small Businesses
ISO 27001:2022 Implementation: From Start to Finish with Case Study
Define Your ISMS Scope and Context
To establish your Information Security Management System (ISMS), you must first define its boundaries. Decide whether your ISMS will encompass the entire organization or focus on specific departments, locations, or processes. Keep in mind that ISO 27001 certification applies only to what is outlined within your ISMS scope, as described in your certification.
Begin by examining both internal and external factors that influence your security landscape. Internally, consider areas like where sensitive information is handled, your IT infrastructure, and your organizational structure. Externally, think about regulatory requirements like GDPR, market dynamics, and current threats such as phishing or ransomware attacks. This evaluation is a requirement under Clause 4.1 of ISO 27001 and serves as the groundwork for your ISMS.
You’ll also need to assess dependencies and interfaces - the points where your protected information interacts with third parties or external entities. For instance, if you rely on a cloud service provider or share customer data with a payment processor, these connections must be clearly documented. Additionally, identify any areas or processes that will not be included in your ISMS and explicitly note these exclusions. Once your scope is defined, the next step is to catalog assets critical to your operations.
Identify Critical Assets
The first actionable step in defining your ISMS scope is creating an inventory of your critical assets. These assets generally fall into four categories:
- Information assets: Customer data, intellectual property, and other sensitive business information.
- Physical assets: Laptops, servers, mobile devices, and office locations.
- Intangible assets: Brand reputation and intellectual property rights.
- Supporting assets: IT systems, hardware, facilities, and personnel.
After listing these assets, prioritize them based on their sensitivity and importance to your business operations. This ranking will guide how you protect each asset. Assign an owner to every asset - someone who is responsible for its classification, security, and management.
Julia Heron from ISMS.online explains: "The owner is not necessarily the legal or physical holder of the asset but the person that has the responsibility and matching authority to ensure that... assets are correctly classified and protected".
Define Stakeholders and Requirements
Under Clause 4.2 of ISO 27001, you must identify all relevant stakeholders and their security expectations. Stakeholders can include customers, regulators, suppliers, employees, and shareholders. For each group, document their specific security requirements, such as contractual obligations, regulatory compliance, or service-level agreements (SLAs).
It’s a good practice to regularly engage with stakeholders - through interviews or other methods - to ensure their security needs are up to date. Use this information to create an ISMS Scope document. This document should clearly outline the products, services, locations, departments, and networks included in your ISMS. It will act as a detailed guide for your risk assessments and control measures. For small businesses, developing this document and becoming audit-ready typically takes around four months.
Secure Leadership Commitment and Establish Policies
Implementing ISO 27001 without the backing of senior management is a recipe for failure. Leadership plays a key role in providing the necessary resources and embedding security as a fundamental business priority.
"The commitment of top management is crucial. Their active participation not only allocates necessary resources but also instils a culture of security throughout the organisation." - ISMS.online
To gain leadership support, present a well-defined business case. Highlight tangible benefits like improving credibility with partners, gaining a competitive edge, and avoiding costly regulatory penalties. Once management is on board, schedule regular reviews - annually at a minimum, or quarterly for rapidly growing businesses - so leadership can assess ISMS performance and make strategic updates.
Assign Leadership Roles and Responsibilities
Start by drafting a formal project mandate that outlines the ISMS objectives, budget, and timelines for leadership approval. This document not only secures support but also establishes clear accountability. Next, appoint a dedicated ISO 27001 project manager who will oversee compliance efforts across all departments. Their role includes creating a project plan, coordinating teams, and ensuring deadlines are met.
Form an ISMS team with representatives from various departments to ensure organization-wide participation. Define responsibilities for critical areas like security controls, asset management, and risk treatment. Under ISO 27001:2022, maintaining a record of "security roles and responsibilities" is mandatory and will be reviewed during the certification process.
| Leadership Role | Primary Responsibility | ISO 27001 Requirement |
|---|---|---|
| Top Management | Allocating resources, setting strategy, and ISMS objectives | Clause 5.1, 5.2 |
| ISMS Manager | Driving the project, developing policies, and coordinating efforts | Clause 5.3 |
| Executive Committee | Monitoring progress and aligning cross-departmental efforts | Clause 9.3 |
| Risk Owners | Managing and addressing identified security risks | Clause 6.1.2 |
| Internal Auditor | Ensuring ISMS compliance and effectiveness | Clause 9.2 |
Develop Core Security Policies
Your Information Security Policy acts as the cornerstone of your ISMS. This document outlines your organization’s security commitment and sets the direction for achieving your objectives. Leadership must formally approve this policy, and it should be communicated across the organization to establish accountability. When drafting the policy, link your security goals to broader business objectives to showcase its value beyond compliance.
Supplement the main policy with targeted policies that address specific areas like access control, incident response, data protection, and supplier security. While ISO 27001 templates can help streamline the process, customize them to reflect your organization’s unique risks, workflows, and terminology. Collaborate with key stakeholders during development to ensure the policies are practical and widely supported. Finally, make your security objectives measurable by setting quantifiable targets that can be reviewed during management meetings.
These policies lay the groundwork for conducting thorough risk assessments and implementing effective controls within your ISMS.
Conduct Risk Assessment and Risk Treatment
Risk assessment is where ISO 27001 compliance becomes actionable. It's about systematically identifying, evaluating, and addressing risks in a structured way.
Start by defining a risk methodology - essentially, a framework for measuring threats. For small businesses, simplicity is key. A straightforward 3x3 or 5x5 matrix that evaluates risks based on likelihood and impact is not only effective but also easier to explain during audits.
"Auditors value a risk assessment that is consistent, clear, and repeatable over one that looks mathematically sophisticated but is difficult to explain." – Chill Compliance
Once the methodology is in place, identify all information assets within your organization. This includes digital assets like databases, physical assets such as laptops and servers, and intangible ones like intellectual property or critical personnel. Then, pinpoint potential threats (e.g., phishing, ransomware, theft) and vulnerabilities (e.g., unpatched software, weak passwords, lack of multi-factor authentication). Assign a numerical score to each risk based on how likely it is to occur and its potential impact on confidentiality, integrity, or availability.
After scoring the risks, decide how to address each one. You have four options: mitigate (apply controls like multi-factor authentication), transfer (use cyber insurance), avoid (stop using high-risk systems), or accept (live with low-impact risks that fall within acceptable limits). Document these decisions in a Risk Register, a Risk Treatment Plan, and a Statement of Applicability that explains why specific Annex A controls were chosen or excluded [20,21].
Perform a Risk Assessment
With your methodology in hand, conduct a detailed assessment. Focus on high-value systems and data - customer databases, financial records, or code repositories - that could cause the most damage if compromised. This approach ensures you’re prioritizing resources effectively and not wasting time on minor risks while critical ones remain unaddressed.
For each asset, identify threats and vulnerabilities, then use your matrix to calculate risk scores. For example, a phishing attack targeting the finance team might score 4 for likelihood and 5 for impact, giving it a total risk score of 20. Compare these scores to your Risk Acceptance Criteria, which outlines what leadership considers tolerable [22,3].
| Likelihood Level | Description | Numerical Value |
|---|---|---|
| Highly Likely | Expected to occur frequently (e.g., monthly) | 5 |
| Likely | Probable to occur (e.g., once a year) | 4 |
| Possible | Might occur at some point | 3 |
| Unlikely | Not expected to occur | 2 |
| Highly Unlikely | Only in exceptional circumstances | 1 |
Assign ownership to every identified risk. For instance, the engineering team might handle server vulnerabilities, while the CEO oversees decisions about high-level risk acceptance. Use a centralized Risk Register to keep everything organized and traceable for audits.
Develop and Implement Risk Treatment Plans
For risks that exceed your organization’s tolerance levels, create a Risk Treatment Plan. This document outlines specific steps to address each vulnerability and is a must-have for audits [12,21]. Link each action to a corresponding Annex A control to show how you’re managing the risk.
| Risk Treatment Option | Action Taken | Example for Small Business |
|---|---|---|
| Mitigate (Reduce) | Apply controls to lower likelihood or impact | Implementing Multi-Factor Authentication (MFA) |
| Avoid | Change or stop the activity causing the risk | Discontinuing use of a high-risk legacy system |
| Transfer (Share) | Shift risk to a third party | Purchasing cyber insurance or using a secure cloud provider |
| Accept (Retain) | Acknowledge the risk without further action | Accepting a low-impact risk that costs more to mitigate than the potential loss |
After implementing controls, evaluate the remaining (residual) risk to ensure it meets your acceptance criteria. For example, if adding MFA reduces a phishing risk score from 20 to 6 and your threshold is 8, the risk is now within acceptable limits. Be sure to document these residual risks in your Risk Treatment Plan.
Review your risk assessments annually or whenever major changes occur - such as migrating to a new cloud platform or dealing with a security incident. This keeps your Information Security Management System (ISMS) aligned with evolving risks. For many small and medium-sized businesses, achieving audit readiness for ISO 27001 typically takes around four months.
sbb-itb-b92d866
Implement Annex A Controls Checklist
Once you've completed your risk assessment and treatment, the next step is implementing the relevant Annex A controls that address the risks you've identified. The ISO 27001:2022 standard outlines 93 controls, grouped into four themes: Organizational, People, Physical, and Technological. However, you only need to apply the controls that align with your specific risk profile, as outlined in your Statement of Applicability (SoA).
"ISO 27001:2022 recognises that each organisation has unique information security needs and challenges. One of the standard's strengths is its flexibility, particularly when implementing Annex A controls." - ISMS.online
Start by focusing on controls that address your most critical risks. For example, prioritize securing endpoint devices (A.8.1), managing privileged access (A.8.2), and ensuring regular data backups (A.8.13) as part of your core technological safeguards. If your organization already complies with standards like SOC 2, you can map your existing controls to ISO 27001 to avoid duplicating efforts.
Assign a control owner for each measure and clearly define roles (e.g., A.5.2) to maintain accountability. Compliance automation platforms can simplify this process by tracking progress and gathering audit evidence automatically - potentially automating up to 80% of the manual work required for certification. Regularly review your controls, at least annually or whenever significant changes occur, to ensure they remain effective against new and emerging threats. This structured approach ties your risk treatment plans directly to actionable control implementation.
Information Security Policies (A.5)
Your organization's Information Security Policy serves as the foundation for all other controls. Building on leadership's directives, create a clear and accessible policy that demonstrates your commitment to safeguarding information assets. This policy should be approved by leadership and communicated to all employees. Supplement it with specific policies addressing areas like access control, cryptography, incident management, and asset classification.
Under A.5.1 (Policies for Information Security), develop and distribute security guidelines tailored to your organization's risks. While templates can be helpful, make sure your policies reflect your unique needs. Appoint an Information Security Officer (A.5.2) with clear reporting responsibilities, and maintain an inventory of assets (A.5.9) that includes all hardware, software, and critical data, along with assigned owners.
Implement a data classification system (A.5.12) to label information based on its sensitivity - such as Public, Internal, or Confidential - so employees know how to handle it appropriately. Establish an incident management procedure (A.5.24) to address and report security events effectively. Additionally, ensure your ISMS undergoes an independent review (A.5.35) annually as part of a structured audit plan.
Access Control (A.9)
Access control is key to ensuring that only authorized individuals can access specific systems and data. Implement measures like Role-Based Access Control (RBAC) and Multi-Factor Authentication (MFA) to enforce the principle of least privilege, ensuring users only have access to what they need for their roles.
Set up a process for creating, modifying, and removing user accounts. Integrate this process with your HRIS to flag risky accounts, such as those belonging to terminated employees or individuals who have changed roles. Conduct regular access reviews - quarterly, for example - and use pre-built connectors to consolidate access data for easier audits. Automated workflows can further streamline the process by assigning access changes to designated owners and logging all updates for compliance purposes.
In October 2024, Equalture, a software company based in the Netherlands, achieved ISO 27001 compliance in just eight weeks using the Sprinto automation platform. Under the guidance of CTO Jaap Haagmans, the company automated evidence collection and policy management, eliminating the need to answer over 160 manual security questions.
"We saw that if you answered 'no' to the question, 'Are you ISO 27001 certified?', about 160 more questions came up... Now it's really convenient for us to say 'yes we're ISO compliant'." - Jaap Haagmans, CTO, Equalture
These access control measures strengthen your overall security framework and ensure compliance with ISO 27001 standards.
Cryptography (A.10)
Cryptography plays a critical role in protecting both in-transit and at-rest data, as highlighted in your risk treatment plans. Use TLS 1.2 (or higher) for secure web communications and email protocols, and enforce full-disk encryption on company laptops and sensitive databases.
Implement a formal key management system that covers key generation, storage, and revocation, while documenting the entire lifecycle. Your cryptography policies should outline acceptable encryption standards and explicitly prohibit outdated methods. Review these policies annually to ensure they stay up to date with the latest threats and technologies.
For organizations operating entirely remotely, physical entry controls may not be applicable. In such cases, you can justify their exclusion in your SoA while focusing on other relevant controls. By taking these steps, you ensure that your cryptographic measures align with ISO 27001 requirements and effectively safeguard sensitive information.
Monitor, Audit, and Improve Your ISMS
Getting ISO 27001 certification isn't the end goal - it's just the beginning of maintaining and enhancing your organization's security practices. The standard requires ongoing efforts to monitor your ISMS, conduct regular audits, and make improvements based on findings. This continuous cycle ensures your controls remain effective as your business grows and evolves. Here's how to approach monitoring, auditing, and improving your ISMS.
Set Up Monitoring and Measurement
Start by defining Key Performance Indicators (KPIs) to evaluate how well your security controls are working. Clause 9.1 of the standard emphasizes the need for clear metrics to assess both individual controls and the overall ISMS. Examples include tracking the number of security incidents each quarter, the percentage of employees completing security training, or the average time it takes to address critical vulnerabilities.
Continuous monitoring is essential for identifying issues before they escalate. Assign process owners to manage evidence and maintain readiness. Keep a detailed audit trail of activities like training sessions, access reviews, and incident responses.
Using compliance automation tools can significantly reduce the manual effort involved in monitoring - by as much as 80% - allowing your team to focus on strategic improvements instead of administrative tasks. Dashboards that provide real-time data on control performance can help you quickly identify trends and address weaknesses.
Once you've established monitoring, the next step is to verify your controls through structured internal audits.
Conduct Internal Audits
Internal audits, as outlined in Clause 9.2, are a proactive way to identify and resolve issues before external auditors get involved. Schedule these audits regularly and ensure they're conducted by independent auditors - either internal team members who weren't part of the ISMS implementation or external consultants. This independence ensures an unbiased assessment.
Appoint a lead auditor at least a month in advance to allow time for planning and reviewing documentation. Begin with an opening meeting to confirm the audit's scope, objectives, and criteria with management. Use sampling techniques to make the process efficient.
"Internal audits should verify the effectiveness of your business's information security posture, while also unearthing additional precautions to be put in place if necessary." - Hicomply
When reviewing audit findings, categorize them as either nonconformities (issues that must be corrected to meet requirements) or opportunities for improvement (ways to enhance efficiency). Document all findings in a formal ISMS audit report and present them to senior leadership during management reviews. Conduct a self-assessment before your formal certification audit to address any weaknesses and refine your ISMS.
Implement Improvement Processes
Adopt the Plan-Do-Check-Act (PDCA) model to guide your security improvements. The "Act" phase is particularly important for addressing audit findings and incident data. Use Clause 10.1 to document nonconformities and implement corrective actions.
Prioritize improvements based on their potential risk and the resources available. Assign ownership for each identified gap or risk treatment activity, and set clear deadlines to ensure accountability. Treat your Statement of Applicability as a dynamic document - update it whenever risk assessments or business needs change.
"Achieving ISO 27001 certification is a major milestone, but it's just the beginning. Establish a continuous improvement cycle to keep strengthening your Information Security Management System (ISMS)." - Kyle Morris, Head of GRC, Scytale
Senior leadership must conduct management reviews (Clause 9.3) at least annually - or even quarterly if your business operates in a fast-changing environment. These reviews evaluate ISMS performance, analyze audit results, and allocate resources for strategic improvements. After certification, your organization will undergo annual surveillance audits by your certification body to confirm your ISMS remains effective over the three-year certification period. Ensure you maintain evidence of corrective actions to demonstrate your ISMS is not only compliant but also continuously evolving. This ongoing improvement strengthens the foundation you've built and supports long-term success.
Use ISMS Copilot to Simplify Compliance
For small businesses, keeping up with ISO 27001 compliance can feel like an uphill battle, especially when handling it manually. That’s where ISMS Copilot comes in, taking the weight off your shoulders by automating the most tedious parts of implementation and maintenance. In fact, it can cut manual workloads by up to 80%. This means your team can spend more time improving security strategies rather than getting buried in administrative tasks.
ISMS Copilot is packed with tools designed to make compliance less of a headache. For instance, the Risk Assessment Assistant helps you identify key information assets, potential threats, and vulnerabilities. It uses a systematic approach that aligns with ISO 31000:2018 principles, ensuring your risk assessments are clear, prioritized, and in line with global standards. On top of that, the Policy Generator Assistant simplifies creating critical documents like Information Security and Risk Management Policies, tailoring them to your specific risk assessment results.
Staying compliant over time can be just as challenging as getting there, but ISMS Copilot has you covered. It automates evidence collection from tools you already use - like Microsoft 365, Slack, and various cloud platforms - eliminating the need for manual data gathering. The platform also keeps an eye on your controls, sending real-time alerts to ensure your ISMS is always audit-ready, not just during periodic checks [33, 11].
To strengthen internal oversight, ISMS Copilot includes built-in audit tools. These come with pre-made templates and gap analysis features that compare your current controls against the latest ISO 27001:2022 requirements. You can even run mock audits to catch and fix nonconformities before an external audit takes place. The platform also generates essential reports, like your Statement of Applicability, automatically - saving you time and ensuring both internal and external auditors get exactly what they need.
Collaboration is seamless with ISMS Copilot. Version control tracks all policy updates for audit purposes, and team members can work on documentation together in real time [31, 7]. Plus, by integrating with your existing tools, the platform minimizes the learning curve and makes task delegation easier. These features work together to keep your ISMS running smoothly and ready for audits, all while supporting your broader ISO 27001 compliance goals.
Conclusion
Achieving ISO 27001 compliance is entirely within reach for small businesses. By taking a step-by-step approach - defining the scope of your ISMS, securing leadership buy-in, conducting detailed risk assessments, implementing Annex A controls, and prioritizing continuous monitoring - you create a solid framework for protecting your information assets. This process not only safeguards your data but also builds trust with clients and stakeholders. Plus, it positions your business to secure contracts with larger organizations and government entities.
Although compliance can feel like a daunting task, the investment is well worth it. For small businesses, spending approximately $14,000–$16,000 on certification can open doors to new opportunities and strengthen relationships with stakeholders. Additionally, using compliance automation platforms can cut manual effort by up to 80%, significantly reducing the burden on your team.
"ISO 27001 compliance provides a clear framework for protecting information assets, reducing security risks, and maintaining stakeholder trust." - Mimecast
Tools like ISMS Copilot make the journey even more manageable by automating key tasks such as documentation, risk assessments, evidence collection, and ongoing monitoring. These AI-driven tools guide you through each phase, ensuring you stay aligned with ISO 27001:2022 standards and remain audit-ready throughout the year. This allows your team to focus on improving security strategies instead of getting bogged down by administrative work.
Maintaining certification requires continuous monitoring, but the benefits are undeniable. By following the outlined steps and leveraging tools like ISMS Copilot, your small business can confidently navigate the compliance process and enjoy the competitive edge that ISO 27001 certification provides.
FAQs
What are the main benefits of ISO 27001 certification for small businesses?
ISO 27001 certification offers small businesses a clear framework to protect sensitive data effectively, minimizing the chances of cyberattacks and data breaches. Earning this certification signals a serious dedication to information security, which can build customer confidence and help businesses distinguish themselves in a crowded marketplace.
Beyond trust-building, ISO 27001 compliance can unlock new opportunities by meeting the security expectations of clients and partners who prioritize working with secure suppliers. It also helps businesses refine their internal processes, manage risks more effectively, and align with regulatory standards - reducing the risk of expensive disruptions. In essence, it boosts security, trustworthiness, and operational stability for small businesses.
What are some effective ways for small businesses to save time and money when achieving ISO 27001 compliance?
Small businesses can cut down on both time and expenses when working toward ISO 27001 compliance by using structured checklists and automation tools designed to meet their specific needs. A well-thought-out checklist simplifies the process by breaking it into manageable steps - like performing risk assessments, defining necessary controls, and documenting policies. This approach helps prevent delays and ensures nothing important is overlooked.
Tools like ISMS Copilot, a leading AI solution for ISO 27001, take this a step further by automating repetitive tasks such as risk management, documentation, and ongoing monitoring. This not only reduces manual work but also lowers the chance of errors, helping the process move along more smoothly. By focusing on efficient practices and leveraging the right tools, small businesses can achieve compliance more quickly while keeping costs under control.
Why is leadership important for successfully implementing an ISMS?
Leadership plays a crucial role in effectively implementing an Information Security Management System (ISMS) that aligns with ISO 27001 standards. When leadership is actively engaged, it fosters a company-wide commitment to security, promotes accountability, and ensures that safeguarding information remains a priority.
Strong leaders help establish clear security policies, allocate the right resources, and align security objectives with broader business goals. Their active participation ensures that security becomes part of everyday operations and that all employees clearly understand their roles in maintaining it. Without dedicated leadership, maintaining compliance becomes a struggle, and the organization may face heightened risks.

