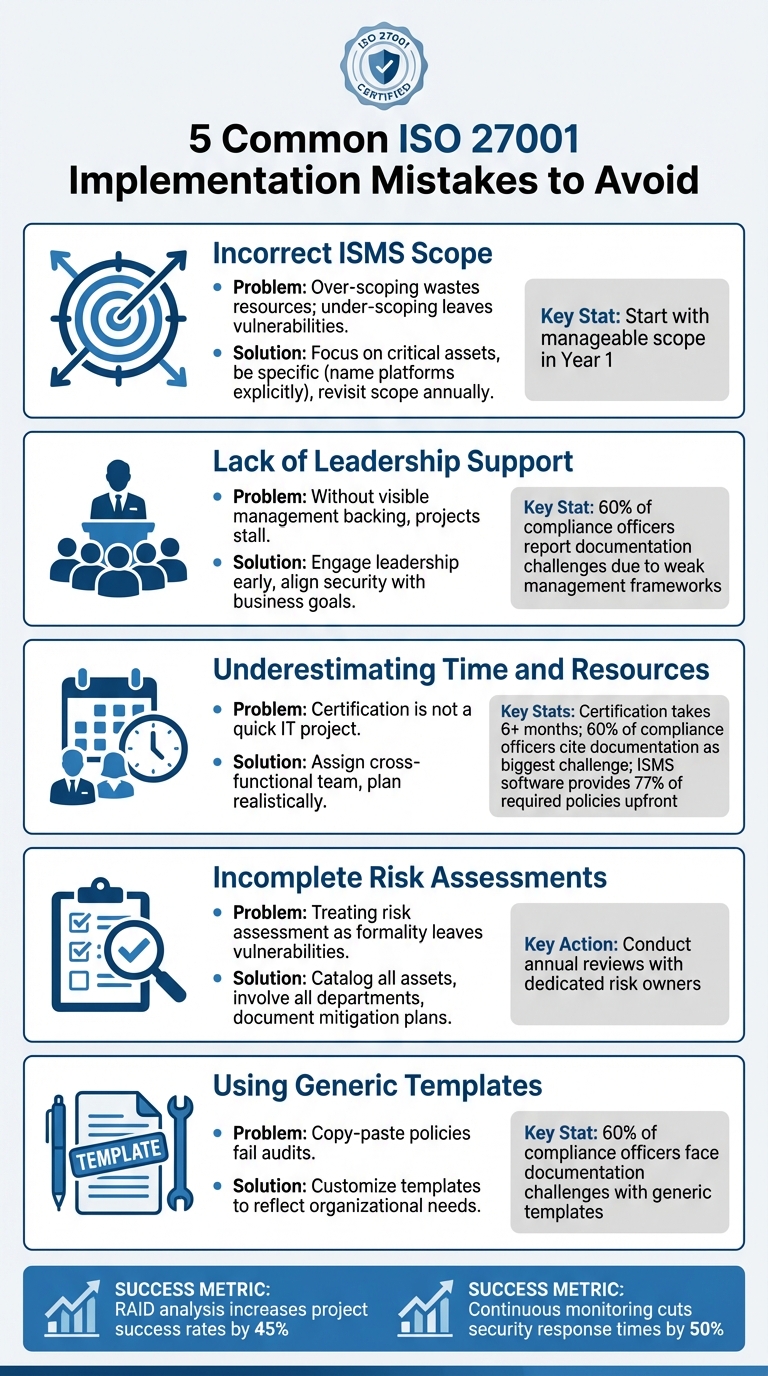
5 Common ISO 27001 Implementation Mistakes to Avoid
ISO 27001 certification can help safeguard sensitive data and build trust, but many businesses stumble during implementation. Here are five mistakes to avoid:
- Incorrect ISMS Scope: Over-scoping wastes resources; under-scoping leaves vulnerabilities. Focus on critical assets and revisit the scope annually.
- Lack of Leadership Support: Without visible management backing, projects stall. Engage leadership early and align security with business goals.
- Underestimating Time and Resources: Certification often takes 6+ months. Assign a cross-functional team and plan realistically.
- Incomplete Risk Assessments: Treat risk assessments seriously - catalog assets, involve all departments, and document mitigation plans.
- Using Generic Templates: Templates should be customized to reflect your organization’s specific needs. Avoid "copy-paste" policies.
5 Common ISO 27001 Implementation Mistakes and How to Avoid Them
Top 10 Mistakes When Implementing ISO/IEC 27001
sbb-itb-b92d866
1. Defining the ISMS Scope Incorrectly
Getting the scope of your ISMS right is a critical first step - and one that’s often misunderstood. The scope sets the boundaries: everything within it must adhere to the ISMS, while anything outside is exempt. The challenge? Many organizations either cast the net too wide or keep it too narrow.
"Defining the right scope requires a critical balance. Overreaching can dilute your efforts, leading to wasted resources, while too narrow a focus might leave critical areas unprotected." - Insight Assurance
Over-scoping - trying to include the entire organization from the start - can quickly overwhelm your team. It’s a recipe for wasted resources, frustration, and, more often than not, failure. On the other hand, under-scoping can leave essential systems and data exposed, creating vulnerabilities that auditors are sure to flag.
A smarter approach? Start with a focused, manageable scope. For the first year, zero in on the services and technologies that are directly tied to customer success - think core platforms, customer data processing, and the systems supporting them. For SaaS companies, this might mean focusing on product design, development, hosting, and support, rather than trying to include every department.
Be specific. Avoid vague terms like "cloud services." Instead, name the platforms explicitly: "AWS (US-East region)", "Microsoft 365", or "HubSpot CRM". Don’t forget to document what’s out of scope with clear justifications. If you can’t explain why something is excluded, it probably shouldn’t be. And remember, if remote workers access in-scope data, their home offices must meet the same security requirements as your main office - VPNs and endpoint policies included.
Finally, commit to revisiting your scope annually. As your business evolves, so should your ISMS.
With a clear and well-defined scope, you’ll be ready to tackle the next step: securing strong leadership support.
2. Missing Leadership Support
ISO 27001 is far more than just an IT initiative - it’s a transformative shift in how a business approaches information security. Without strong, visible backing from top management, even the most well-designed Information Security Management System (ISMS) can lose traction. Clause 5 of the standard makes this clear, requiring leadership to actively demonstrate their commitment by defining security policies, providing necessary resources, and taking responsibility for the ISMS’s success. When leadership visibly supports the initiative, the entire organization is more likely to align with its objectives.
"Without visible management support, most ISO 27001 projects stall." - GRC Solutions
A lack of leadership involvement often results in telltale issues: struggles to secure adequate budgets and staffing, declining project momentum, and executives viewing the ISMS as a mere compliance exercise rather than a strategic priority. In fact, 60% of compliance officers report that documentation challenges frequently arise due to weak management frameworks.
When leadership is truly engaged, the perception of security evolves from being an IT silo to a shared organizational responsibility. This commitment leads to better resource allocation, faster decision-making, and even catches the attention of auditors who value leadership’s active role in management reviews.
To gain executive buy-in, it’s essential to frame the conversation in terms of business impact. Present a clear case for the return on investment, emphasizing reduced risks of data breaches, avoidance of costly fines under regulations like GDPR or HIPAA, competitive advantages in securing contracts, and stronger customer trust. Share compelling industry examples that demonstrate the consequences of inadequate data protection, and involve leadership early to align the ISMS with broader business goals. With top-level support firmly in place, you’ll be better equipped to tackle the challenges ahead, ensuring the necessary time and resources are available to see the project through.
3. Underestimating Time and Resources
Some organizations mistakenly view ISO 27001 certification as a quick IT project that can be completed in just a few weeks. However, the reality is much more complex. Achieving certification typically takes six months or more, according to ISO auditors. And that’s assuming you have the right people, sufficient budget, and strong cross-departmental support from the start.
Relying on just one or two people to manage the process often creates bottlenecks that can derail the entire effort. IT Governance highlights this common pitfall:
"Projects fail when organisations underestimate the effort required to develop, implement and maintain an ISMS. Typical mistakes include insufficient staff assigned to the project, unrealistic timelines and lack of subject expertise".
To succeed, organizations need a well-structured plan and a realistic understanding of the resources required.
Take Mesh-AI as an example. In 2024, the company achieved ISO 27001 certification in just six months by using a centralized platform to distribute compliance tasks. Tom Mahoney, their Operations & Staffing Director, spearheaded the project by involving the HR department directly in compliance efforts. This approach avoided the common mistake of overburdening a small IT team. By sharing the workload across departments, Mesh-AI transitioned from a basic information security policy to a fully operational ISMS. They earned certification with zero non-conformities during the audit conducted by Alcumus ISOQAR. Their success highlights the importance of accurate resource planning and cross-functional collaboration.
ISO 27001 certification isn’t a one-and-done task - it requires ongoing dedication. You’ll need to schedule internal audits, update risk assessments, and conduct regular management reviews throughout the year. Specialized ISMS management software can make this easier by providing up to 77% of the required policies and controls documentation upfront. But even with automation, you’ll still need committed team members to customize templates, manage dependencies, and ensure the system aligns with your business needs.
Documentation is another major hurdle. In fact, 60% of compliance officers say that managing documentation is one of the biggest challenges to effective compliance. Rushing the process or spreading your team too thin can lead to “compliance theatre,” where you churn out documents that look good on paper but don’t actually reflect how security operates in practice. To avoid this, develop a detailed project plan with clear goals, realistic timelines, and a cross-functional team.
As Mark Sharron, Search & Generative AI Strategy Lead at ISMS.online, aptly puts it:
"If information security management is getting in the way, you are probably doing it wrong".
Next, let’s focus on ensuring your risk assessments are thorough and complete.
4. Conducting Incomplete Risk Assessments
Risk assessment is a cornerstone of ISO 27001, but too often, organizations treat it as a mere formality rather than a meaningful strategy. When done half-heartedly, it can leave glaring vulnerabilities unaddressed, undermining the effectiveness of security controls and creating serious risks.
Skipping a thorough assessment can open the door to data breaches, cyberattacks, and audit failures that jeopardize certification. Even worse, teams may resist security measures if they don’t see clear, practical benefits.
To steer clear of these issues, take a structured approach. Begin by cataloging all information assets - this includes digital files, physical documents, devices, and intellectual property. For each asset, identify specific threat-vulnerability combinations (like the risk of stolen laptops if encryption isn’t enabled). Use a consistent scoring system to evaluate the likelihood and potential business impact of each identified risk.
Don’t limit your assessment to IT alone. Bring in representatives from all departments - HR, Legal, Procurement, and others - to ensure no critical risks are overlooked. Information security silos can lead to blind spots that undermine your overall strategy. Also, assess risks associated with third parties. Many organizations assume their suppliers have strong security measures, only to discover gaps when it’s too late.
"Risk assessment is at the heart of ISO 27001. Skipping this step or conducting it superficially can have severe consequences, leading to the implementation of ineffective or unnecessary controls."
A detailed risk assessment isn’t just about compliance - it’s the foundation for ongoing improvement of your Information Security Management System (ISMS). Make it a priority to conduct annual reviews, assign a dedicated risk owner for each identified threat, and document your mitigation strategies in a formal Risk Treatment Plan. This plan should clearly outline actions, responsibilities, and timelines to ensure accountability and progress.
5. Using Generic Templates Without Customization
Templates might seem like a quick fix for documentation, but relying on them without proper customization can derail your ISO 27001 implementation. Why? They often fail to capture the unique aspects of your organization - its size, industry, or operational complexity. Worse, auditors can easily spot "copy-paste" policies, which could lead to audit findings, delays, or even denial of certification. Using generic templates can result in what’s known as "compliance theatre", where your Information Security Management System (ISMS) appears compliant on paper but falls short in practice.
"Templates should be a starting point, not the finished product." – IT Governance
To avoid these pitfalls, treat templates as rough outlines, not ready-made solutions. Every policy and control must be tailored to address the specific risks identified in your risk assessment. Collaboration is key - engage stakeholders from departments like HR, IT, Finance, and Procurement to ensure the documented procedures align with how your organization actually operates. If your documentation doesn’t reflect real-world processes, auditors will likely flag it as a non-conformity.
Did you know that 60% of compliance officers face documentation challenges, particularly when templates are used without proper adjustments? To sidestep these issues, thoroughly review each template, align every control with your organization’s specific risks, and implement a robust version control system to ensure employees are always working with the most current, customized policies. If your team lacks the expertise to navigate complex areas - like the Statement of Applicability or access control policies - bringing in consultants can be a smart move. By taking the time to customize your documentation, you’ll not only reflect your operational realities more accurately but also stay prepared for audits down the line.
Conclusion
Achieving success with ISO 27001 demands thoughtful planning and precise implementation. The pitfalls we've discussed - choosing the wrong scope, lacking leadership buy-in, underestimating resource needs, performing incomplete risk assessments, and relying on one-size-fits-all templates - can all be avoided with careful preparation and a strong commitment. As GRC Solutions aptly states:
"ISO 27001 projects do not fail because the Standard is unworkable – they fail when organisations make avoidable mistakes".
To make your ISMS a true business asset, start by securing leadership support, fostering collaboration across teams, and defining a scope that fits your organization's needs. Focus on thorough risk assessments and ensure your ISMS is more than just a compliance exercise. Regular audits, continuous monitoring, and ongoing improvement are essential to staying ahead of emerging threats. In fact, using RAID analysis can increase project success rates by 45%, while continuous monitoring can cut response times to security issues by 50%.
A well-designed ISMS isn’t just about meeting compliance requirements - it’s about embedding security into the fabric of your organization. By integrating security practices into daily operations, you can create a culture where safeguarding information becomes second nature, rather than a checklist for auditors.
FAQs
How do I define the right scope for my ISMS?
Defining the scope of your ISMS (Information Security Management System) is all about pinpointing the parts of your organization that require protection and management under ISO 27001. To get started, take a close look at your business context - this includes your goals, legal and regulatory obligations, and what your stakeholders expect from you. Factor in your organization’s assets, locations, and processes, as well as any internal or external elements that might impact your information security.
Once you’ve gathered this information, it’s time to set clear boundaries for your ISMS. Identify what will be covered, such as specific departments, systems, or physical locations, and what will be left out. Aligning the scope with your organization’s key priorities and risks ensures the implementation stays focused and effective, meeting compliance needs without adding unnecessary layers of complexity.
How can I get leadership support for ISO 27001 implementation?
Securing leadership support is essential when implementing ISO 27001. Start by connecting the framework to your organization’s key goals. For instance, emphasize how it helps protect sensitive data, strengthens customer confidence, and ensures compliance with regulatory standards. These connections make it easier for leaders to see how ISO 27001 directly benefits the business.
Get leadership involved early, especially during the scoping and planning stages. This involvement helps them understand their role in setting priorities, allocating resources, and fostering ongoing improvements. Keeping them informed with regular updates about progress and potential risks can further solidify their commitment.
To drive the point home, share real-world examples or data that highlight the impact of leadership involvement. Show how it helps avoid common pitfalls, like underestimating the scope or failing to allocate adequate resources. By tying ISO 27001 objectives to their priorities and showcasing measurable benefits, you can secure the leadership support necessary for a successful rollout.
How can I adapt ISO 27001 templates to fit my organization’s needs?
Adapting ISO 27001 templates to fit your organization means tailoring them to your specific operations and risks. Start by performing a detailed risk assessment to pinpoint threats and vulnerabilities unique to your business. This will guide you in modifying policies, procedures, and controls to accurately reflect your security needs.
Involve key stakeholders from different departments to make sure the templates are realistic, actionable, and aligned with your company's objectives. Avoid relying on generic templates without adjustments; instead, focus on creating documentation that tackles your most pressing risks. Keep the scope focused and flexible, so it can grow with your organization and address new challenges as they arise.
To simplify this process, tools like ISMS Copilot can be a big help, offering streamlined customization while maintaining compliance. Make it a habit to review and update your documentation regularly to account for emerging risks, evolving technologies, and organizational changes.

