ISO 27001 Training: Complete Guide for Beginners
Want to secure your organization's sensitive data? ISO 27001 training is your starting point. This guide covers everything you need to know - what ISO 27001 is, why training matters, and how to get started. Here’s a quick overview:
- What is ISO 27001? An international standard for managing information security through an Information Security Management System (ISMS). It focuses on confidentiality, integrity, and availability of data.
- Why training is important: It’s required under ISO 27001 clauses and helps reduce risks like human error, which accounts for 74% of data breaches.
- What beginners need to learn: Conduct risk assessments, implement security controls, and document your decisions (e.g., the Statement of Applicability).
- Training options: Foundation, Lead Implementer, and Lead Auditor courses, ranging from $575 to $2,770. Self-paced and instructor-led formats are available.
- Tools and resources: Use books, document toolkits, and AI tools like ISMS Copilot to simplify implementation.
Whether you're new to ISO 27001 or looking to deepen your knowledge, this guide provides the steps to protect your organization effectively.
ISO 27001 for Beginners: How to Get Started and Learn ISO 27001
sbb-itb-b92d866
Key Concepts in ISO 27001 Training
Before diving into training courses or certification programs, it's important to grasp the fundamentals of the ISO 27001 framework. At its core, ISO 27001 consists of two main components: Clauses 4 through 10 (the mandatory management requirements) and Annex A (a list of 93 security controls). The clauses provide the structure for your Information Security Management System (ISMS), while Annex A outlines specific safeguards based on your risk assessment.
These components operate within the Plan-Do-Check-Act (PDCA) cycle. Clauses 4–6 focus on planning, 7–8 deal with implementation, 9 emphasizes monitoring, and 10 ensures ongoing improvement. This structure is pivotal because auditors assess your organization against all these requirements, not just the technical controls. The PDCA cycle ties everything together, ensuring a systematic approach to meeting ISO 27001 standards.
Core Clauses of ISO 27001
Clauses 4 through 10 form the foundation of your ISMS. Here’s a quick breakdown of their roles:
-
Clause 4: Context of the Organization
This is where you define your scope, identify stakeholders, and analyze internal and external factors affecting your security. As iso27001.com explains, "If you do not know your terrain, you cannot defend it. Document your context or fail the audit immediately". -
Clause 5: Leadership
Accountability starts at the top. Your CEO and leadership team must actively demonstrate their commitment to information security. This isn’t just a checkbox - auditors may fail your organization if the CEO cannot clearly explain the security policy. -
Clause 6: Planning
This clause drives the process. It includes conducting risk assessments, developing treatment plans, and creating the Statement of Applicability (SoA) - a document that justifies which controls you’ve implemented and why. -
Clause 7: Support
Ensures you have the necessary resources, skilled personnel, and documented processes to maintain your ISMS. -
Clause 8: Operation
This is where you execute your risk treatment plans and put your policies into action. -
Clause 9: Performance Evaluation
Regular monitoring, internal audits, and management reviews ensure the system stays effective. -
Clause 10: Improvement
Focuses on corrective actions and refining your ISMS. As iso27001.com puts it, "A plan without logs is a hallucination", emphasizing the importance of thorough documentation.
Understanding these clauses is essential, as they form the management framework against which your organization will be evaluated.
Annex A Controls
While the clauses set the management structure, Annex A provides a detailed list of 93 security controls, grouped into four domains. The 2022 update streamlined the number of controls from 114 to 93, organizing them as follows:
- Organizational: 37 controls
- People: 8 controls
- Physical: 14 controls
- Technological: 34 controls
You don’t need to implement all 93 controls. Instead, your risk assessment determines which controls are necessary to address your organization’s specific risks. The controls you choose - and those you exclude - must be documented in your Statement of Applicability, along with clear justifications. For example, if your operations are entirely cloud-based, you’ll need to explain why physical controls are not applicable.
The 2022 revision also introduced 11 new controls to address emerging threats. These include Threat Intelligence (A.5.7), Information Deletion (A.8.10), and Data Leakage Prevention, reflecting the rise of cloud services and evolving attack methods. For detailed implementation guidance on these controls, refer to ISO 27002, which serves as a practical companion to ISO 27001.
Documenting and implementing the appropriate controls is a critical step in turning ISO 27001’s framework into actionable security measures.
What Beginners Need to Learn
Once you grasp the basic framework, the real challenge begins. For beginners diving into ISO 27001, the focus should be on three key areas: conducting risk assessments, implementing security controls, and properly documenting decisions. These skills are the backbone of a successful ISMS (Information Security Management System) and will be closely examined during the certification process.
Risk Assessment and Treatment
Risk assessment is the driving force behind your ISMS. It helps you identify threats and allocate resources effectively. Start by listing your information assets, identifying potential threats, and pinpointing vulnerabilities.
During the analysis phase, calculate risk levels by combining the likelihood of an event with its potential impact. Many organizations rely on a 5x5 risk matrix to visualize risks. This approach highlights critical issues that demand immediate action. For example, a risk score between 20 and 25 is considered "Critical" and often requires halting the associated activity until the issue is resolved.
| Risk Level | Score (Likelihood x Impact) | Action Required |
|---|---|---|
| Low | 1–6 | Monitor; no immediate action needed |
| Medium | 7–14 | Address within 6 months to lower the risk |
| High | 15–19 | Address within 3 months as a priority |
| Critical | 20–25 | Act immediately; consider pausing the activity |
Once risks are assessed and treatment options selected, the next step is implementing the relevant controls from Annex A of the standard.
Each risk needs an assigned owner to oversee its management. As Ethan Heller, a GRC expert at Vanta, explains:
"While the core risk assessment requirement for ISO 27001 didn't change with the update to the new 2022 version, it remains crucial to consider a wide range of risks to ensure that the controls your organization applies adequately address your identified security risks".
To streamline your process, group similar assets together when developing your risk register.
Implementing Annex A Controls
After completing your risk assessment, Annex A provides a set of tools to address identified threats. It’s important to note that Annex A isn’t a checklist of mandatory items. Instead, you select only the controls that are relevant to your organization’s specific risks and context.
For detailed guidance, refer to ISO 27002, which offers practical advice on implementing each control. For instance, if your risk assessment highlights concerns around data leakage, you might apply Control 8.12 (Data Leakage Prevention) by following the technical and procedural steps outlined in ISO 27002.
Implementation involves more than just adding technology. It requires well-defined policies, clear procedures, and tools that support your security objectives.
The 2022 update introduced 11 new controls, including Threat Intelligence (A.5.7) and Data Leakage Prevention (A.8.12). Even if a control doesn’t apply to your organization - for example, physical controls in a fully remote workplace - you still need to include it in your Statement of Applicability (SoA) with a clear explanation for its exclusion.
Internal Auditing and Statement of Applicability
Once controls are implemented, ongoing oversight is critical. This is where the Statement of Applicability (SoA) and internal audits come into play. The SoA serves as a map linking your identified risks to the controls you’ve chosen. As ISO consultant Alan Parker puts it:
"The SoA is the map that links your risks to your controls".
This document, required for certification, lists all 93 Annex A controls and specifies which ones are implemented, excluded, or planned. For each control, the SoA must include the control ID, justification for inclusion or exclusion, and its implementation status. For example, instead of vaguely marking a control as "Not Applicable", provide specific reasoning, such as "N/A - we have no on-premise infrastructure; all facilities are co-located."
The SoA isn’t a static document. It should be reviewed at least annually or whenever significant changes occur, such as retiring systems or dealing with security incidents. During audits, this document is closely examined to ensure clear traceability from risks to controls, and auditors will expect detailed justifications for any exclusions. As ISO-Docs emphasizes:
"If the SoA is not prepared well by following the regulatory requirements of ISMS standard, it's impossible for a company to get ISO 27001 certification".
Internal audits complement the SoA by ensuring that your controls are not only documented but also effective in practice. Auditors will check if procedures are being followed, systems enforce policies, and the ISMS is delivering measurable improvements in security.
Where to Find ISO 27001 Training
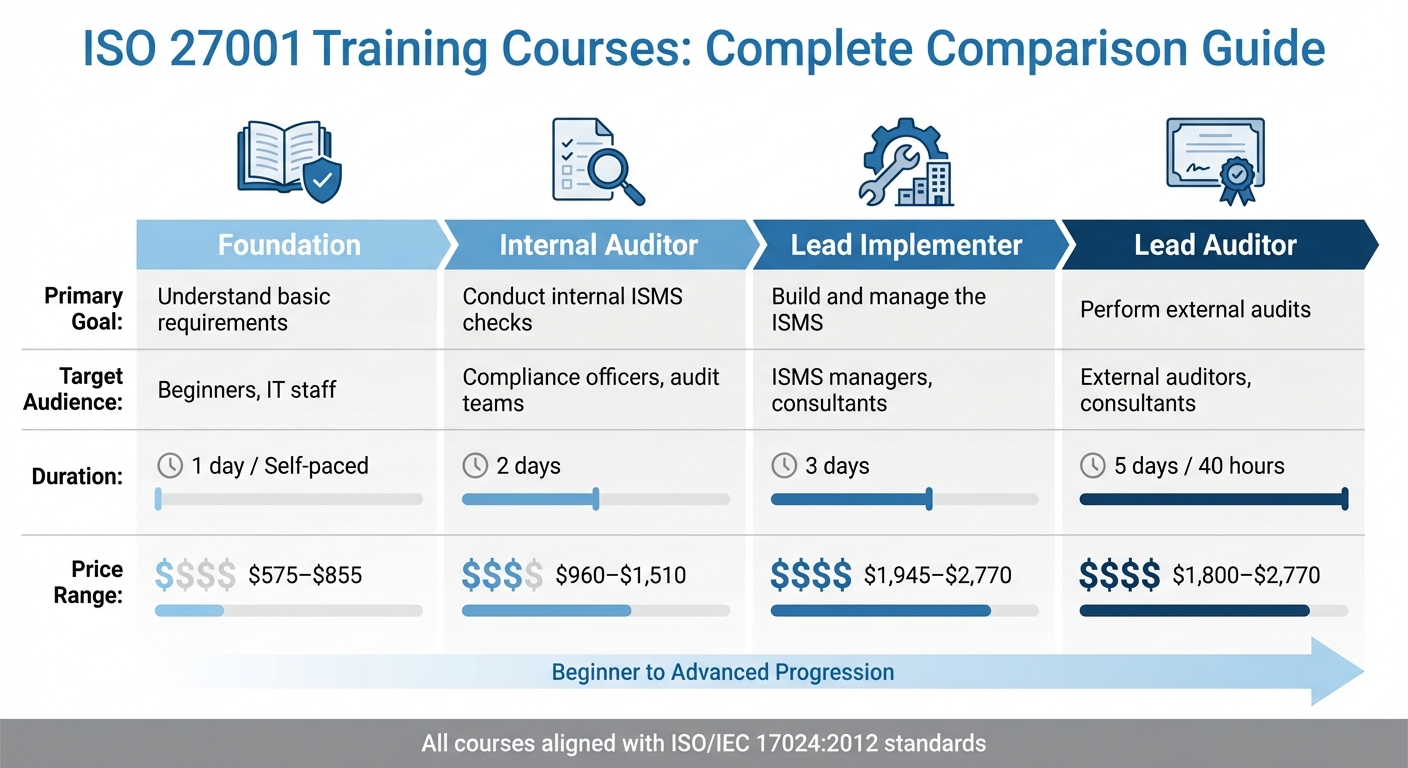
ISO 27001 Training Courses Comparison: Types, Duration, and Costs
Finding the right ISO 27001 training resources is essential for mastering its principles. Whether you're aiming for formal certification, building an Information Security Management System (ISMS), or just learning the basics, there are plenty of options - accredited courses, study guides, and even AI-powered tools.
Accredited Courses and Certifications
If you're looking for formal certification, accredited programs like Lead Implementer and Lead Auditor are excellent choices. These certifications align with ISO/IEC 17024:2012, making them globally recognized by employers.
- Lead Implementer: This course is designed for ISMS managers, consultants, and project leads tasked with creating and managing an ISMS. Typically lasting three days, it costs between $1,945 and $2,770.
-
Lead Auditor: Ideal for those conducting external or certification audits, this course covers ISO 19011 and ISO/IEC 17021 methodologies. It requires at least 40 hours of training and costs between $1,800 and $2,770, depending on the provider. A participant from Roscom Ltd noted:
"The tutor took the time to answer all questions and also did not make us feel like we were asking silly questions, he took his time to give relevant examples".
For beginners, Foundation courses are a great starting point. These one-day programs cost between $575 (self-paced) and $855 (instructor-led). Accredited organizations like IBITGQ, CQI/IRCA, Exemplar Global, and IAS are worth considering.
| Course Type | Primary Goal | Target Audience | Typical Duration | Price Range |
|---|---|---|---|---|
| Foundation | Understand basic requirements | Beginners, IT staff | 1 day / Self-paced | $575–$855 |
| Internal Auditor | Conduct internal ISMS checks | Compliance officers, audit teams | 2 days | $960–$1,510 |
| Lead Implementer | Build and manage the ISMS | ISMS managers, consultants | 3 days | $1,945–$2,770 |
| Lead Auditor | Perform external audits | External auditors, consultants | 5 days / 40 hours | $1,800–$2,770 |
For those who prefer independent learning, books and other resources can be a practical alternative.
Books and Study Guides
Books and study guides offer a flexible way to learn, especially for self-starters or those looking to supplement formal training. A standout resource is the ISO/IEC 27001:2022 - Information Security Management Systems - A Practical Guide for SMEs, published in 2024. It breaks down the 10 core clauses and Annex A controls with real-world examples and FAQs. At CHF 44 (around $49), it's an affordable option.
For a more comprehensive package, the "Information Security - The Basics" bundle includes the official ISO/IEC 27001:2022 standard and the SME handbook. Priced at CHF 179 (approximately $199), it simplifies ISMS implementation for smaller organizations. According to ISO:
"The handbook simplifies the complexities of implementing an Information Security Management System (ISMS) tailored to the unique needs and constraints of SMEs".
If you're taking a do-it-yourself approach, consider a document toolkit like the Iseo Blue DIY Training & Toolkit. Priced at $360, it includes templates for policies, risk assessments, and audit checklists, along with email support for practical guidance. As ISO 27001 consultant Alan Parker explains:
"The course is designed to be a one-stop DIY ISO 27001 solution: learn the concepts, get the templates, follow the steps, ask questions when stuck, and successfully implement".
When choosing study materials, make sure they're updated for the 2022 version of the standard, as it includes key changes to Annex A controls. A hands-on approach - like applying templates immediately after learning a concept - can make the material more actionable.
ISMS Directory and ISMS Copilot
For a centralized way to explore training options, the ISMS Directory is a helpful tool. It allows you to compare accredited providers, consultants, and certification bodies based on location, accreditation, and delivery format - all in one place.
Once you're ready to implement ISO 27001, ISMS Copilot can make the process smoother. This AI assistant simplifies tasks like risk assessments and selecting Annex A controls. Instead of juggling spreadsheets, it offers automated workflows and step-by-step guidance tailored to your organization. It's especially useful for beginners, helping them move from theory to practice without getting bogged down by complex documentation.
How to Complete ISO 27001 Training
ISO 27001 training involves three key steps: understanding the basics, taking structured courses, and applying your knowledge to achieve certification.
Start with the Basics
Before diving into formal training, it's helpful to revisit the ISO 27001 framework and identify where your current practices might fall short. A gap analysis can help you compare your organization's security measures against the standard's requirements, highlighting areas that need improvement. Early on, you'll also need to define the scope of your Information Security Management System (ISMS) - deciding which assets, employees, and locations will be covered. Tim Blair, Sr. Manager at Vanta, offers this advice:
"The trick is crafting a Scope Statement for your ISO 27001 certification that provides value for your customers and includes relevant systems and processes within the scope".
If you're planning to tackle ISO 27001 on your own, keep your approach straightforward. A course like the Iseo Blue DIY Online Course (£285 + VAT, about $360) provides document templates and email support. Alan Parker, the course's founder, reassures small businesses:
"ISO 27001 for smaller businesses doesn't need a lot of expertise – with the right guidance, you can implement it yourself".
Once you've reviewed the basics and identified gaps, you're ready to move on to more detailed training.
Enroll in Structured Courses
Structured courses provide the in-depth knowledge needed to apply ISO 27001 effectively. Foundation courses, available in both self-paced and instructor-led formats, offer a solid introduction to the standard. If you're directly involved in implementing ISO 27001, a Lead Implementer course will cover critical topics like risk assessment, internal audits, and creating essential documents like the Statement of Applicability (SoA).
To maximize what you learn, apply each lesson immediately. For example, after learning about risk assessments, update your risk register using available templates. Before your certification audit, conduct an internal audit to identify and address any remaining gaps. Auditors will expect to see key documents such as your ISMS Scope, Information Security Policy, Risk Assessment Report, and SoA.
Get Certified and Plan Implementation
After completing your training, the next step is certification. Certification is valid for three years but requires annual surveillance audits. Tools like ISMS Copilot can simplify tasks like documentation and risk assessments, saving time and effort. The certification process itself includes two stages: Stage 1, where your documentation is reviewed, and Stage 2, which assesses how effectively your ISMS operates.
In February 2025, the software company Talk Think Do used an AI Copilot agent to streamline their ISO 27001:2022 recertification. Led by Louise Clayton, the team saved over 65 hours of manual work and passed their three-year reaccreditation with zero minor non-conformances. Louise shared:
"AI can't replace governance, context or judgement... But when trained appropriately, it can dramatically accelerate the process and free up time to focus on higher-value work".
Maintaining your certification requires ongoing effort. ISO 27001 emphasizes continuous improvement, often guided by the Plan-Do-Check-Act (PDCA) cycle. Regular refresher training - every 6 to 12 months - is also essential. This not only reinforces a strong security culture but can reduce employee-related cyber incidents by up to 72%.
Next Steps
Now that you've got a solid understanding of ISO 27001's framework, training options, and certification process, it's time to take action. Start with a gap analysis to identify where your security practices excel and where they fall short. At the same time, define the scope of your ISMS. Decide which information assets, systems, and locations you’ll include - keeping it manageable is key. Once your gap analysis is complete, align leadership support with your training strategy.
Get leadership on board. ISO 27001 is driven from the top, and auditors will expect active involvement from your organization’s leadership team. After securing executive backing, choose the training option that fits your needs. For smaller teams with tighter budgets, a DIY course like Iseo Blue’s (priced around $360) offers templates and email support to walk you through the implementation process. If you need a deeper dive, look into advanced training that covers risk assessment, internal audits, and detailed documentation.
Take a hands-on approach. For example, after completing a module on risk assessment, update your risk register and document relevant Annex A controls in your Statement of Applicability. This "learn as you go" method helps turn theoretical knowledge into real-world progress. To save time on documentation and risk assessments, tools like ISMS Copilot can help you focus on more critical tasks.
Finally, commit to ongoing improvement. Regular training and onboarding are essential. Train new hires as part of their onboarding process and refresh your team’s knowledge every 6–12 months. An ISMS isn’t static - it requires continuous evaluation and updates. With the right tools and a clear plan, even smaller businesses can tackle ISO 27001 implementation without needing extensive expertise.
FAQs
What are the main benefits of achieving ISO 27001 certification for an organization?
ISO 27001 certification brings a range of benefits to organizations. One of the biggest advantages is improving information security management, which helps safeguard sensitive data against breaches and cyberattacks. By identifying potential risks and addressing them proactively, it creates a safer operational environment.
It also enhances an organization's reputation and builds trust with clients, partners, and stakeholders. Certification signals a strong commitment to internationally recognized information security standards, which can set a business apart in a competitive market. On top of that, aligning with ISO 27001 can simplify compliance with regulatory requirements, ultimately saving both time and resources.
How can I choose the best ISO 27001 training course for my needs?
Picking the right ISO 27001 training course comes down to your goals, experience, and how you like to learn. If you're just starting out, focus on courses that clearly explain the basics of the standard and its requirements. For those who need flexibility, online self-paced courses are a solid option. On the other hand, if you value interaction and real-time feedback, instructor-led or virtual classes might be a better fit.
Make sure the course content is up-to-date with the latest ISO/IEC 27001:2022 standard. It's also worth checking if the training includes practical resources like tools, templates, or guidance for implementation. Go with a trusted provider that offers courses designed to match your certification goals and learning style. This way, you’ll gain the knowledge and confidence to build and manage an effective ISMS.
What challenges do beginners commonly face when implementing ISO 27001?
Beginners often face a variety of challenges when trying to implement ISO 27001. For starters, the sheer volume of documentation required can feel daunting, especially for those new to the standard’s intricate processes. It’s not just about paperwork - it’s about understanding and aligning with a structured framework that may seem overwhelming at first.
Another big obstacle? Gaining solid support from top management. Leadership buy-in is absolutely essential, as it ensures proper resource allocation and helps align the implementation with the company’s broader goals. Without backing from decision-makers, the process can easily stall.
Then there’s the issue of resources. Limited budgets or not enough staff can make it tough to dedicate the time and expertise needed to implement the standard effectively. On top of that, weaving ISO 27001 into everyday operations without disrupting workflows can be tricky. Many organizations also struggle to see it as more than just a compliance checkbox, which can lead to a lack of genuine engagement.
To tackle these hurdles, it’s crucial to focus on thoughtful planning, secure leadership commitment, and actively engage employees. These steps can help lay the groundwork for a smoother and more meaningful implementation process.

