ISO 27001 Change Management and Risk Integration
ISO 27001 connects change management with risk management to ensure security is maintained during organizational changes like system updates or role adjustments. The standard emphasizes structured planning, risk assessments, and controlled execution to minimize vulnerabilities.
Key takeaways:
- Clause 6 focuses on planning, identifying risks, and creating treatment plans.
- Clause 8 ensures risks are managed during implementation and continuously monitored.
- Changes are categorized into Standard, Normal, and Emergency types, each requiring different levels of assessment and approval.
- Tools like Jira and ServiceNow can streamline processes by linking change requests to risk registers and automating documentation.
What does ISO 27001 Clause 8 say about change management? #iso27001
ISO 27001 Requirements for Change and Risk Management
ISO 27001 ties change and risk management into a unified process, ensuring that planning transitions seamlessly into execution and ongoing evaluation. This is achieved through two key clauses: Clause 6 (Planning) and Clause 8 (Operation). Together, they form the backbone of an effective Information Security Management System (ISMS).
Clause 6: Planning and Risk-Based Thinking
Clause 6 outlines how organizations should identify, evaluate, and address information security risks.
Under Clause 6.1, organizations are required to establish risk criteria - essentially defining how to measure the likelihood and impact of risks. This involves identifying vulnerabilities and threats to key security elements. Once risks are identified, Clause 6.1.3 specifies four treatment options:
- Treat: Implement controls to reduce the risk.
- Transfer: Shift the risk through insurance or outsourcing.
- Avoid: Stop the activity causing the risk.
- Accept: Choose to live with the risk after careful consideration.
This process results in the creation of two critical documents: the Risk Treatment Plan and the Statement of Applicability (SoA). The SoA lists which Annex A controls are implemented and explains any exclusions.
Clause 6.3 (Planning of Changes) introduces a structured approach to modifying the ISMS. Cyberzoni explains, "Clause 6.3 of ISO 27001:2022, titled 'Planning of Changes,' mandates that organizations implement changes to their Information Security Management System (ISMS) in a structured and deliberate manner". This ensures security is prioritized during changes like software updates, cloud migrations, or vendor integrations.
| Clause | Focus | Key Output/Requirement |
|---|---|---|
| 6.1 | Risk Management | Risk Register, Risk Treatment Plan, and Statement of Applicability (SoA) |
| 6.2 | Security Objectives | Measurable goals and plans to achieve them (e.g., "100% staff training completion") |
| 6.3 | Change Planning | Systematic process for ISMS modifications to prevent security gaps |
To comply with Clause 6, organizations should define thresholds for changes, distinguishing between "significant" changes (which require formal risk assessment and management approval) and "minor" changes (which can follow a streamlined process). Keeping a detailed change log is also critical for audit purposes.
Once the risk treatment plan is in place, the focus shifts to implementing and monitoring these controls in daily operations.
Clause 8: Operational Planning and Control
Clause 8 takes the plans from Clause 6 and translates them into actionable steps. Alan Parker, an ISO 27001 consultant, sums it up well:
Clause 8 essentially says: do what you planned to do about risks, and do it in a managed way.
Clause 8.1 (Operational Planning and Control) requires organizations to set criteria for security processes and execute risk treatments in a controlled manner. It also emphasizes the importance of managing planned changes and evaluating the effects of unexpected changes, taking corrective action when needed.
Clause 8.2 (Information Security Risk Assessment) ensures that risk management remains dynamic, requiring assessments at regular intervals or whenever significant changes occur. For example, if your organization migrates to AWS but waits until the annual review to update the risk register, auditors could flag this as a Major Non-Conformity. This clause ensures that operational changes are reflected in ongoing risk assessments.
Clause 8.3 (Information Security Risk Treatment) focuses on the continuous application of the risk treatment plan. It ensures that controls remain active and are updated as new risks arise from operational changes.
To meet Clause 8 requirements, categorize changes into three types:
- Standard: Low-risk, pre-approved changes.
- Normal: Changes requiring full risk assessment and approval.
- Emergency: Urgent fixes with a post-implementation review.
As Iseo Blue advises:
Every change to systems, infrastructure and applications should be planned, reviewed, tested, approved and documented so you don't accidentally introduce outages or security holes.
Testing significant changes in non-production environments and maintaining complete records are essential for audit readiness.
How to Integrate Change Management into Risk Processes
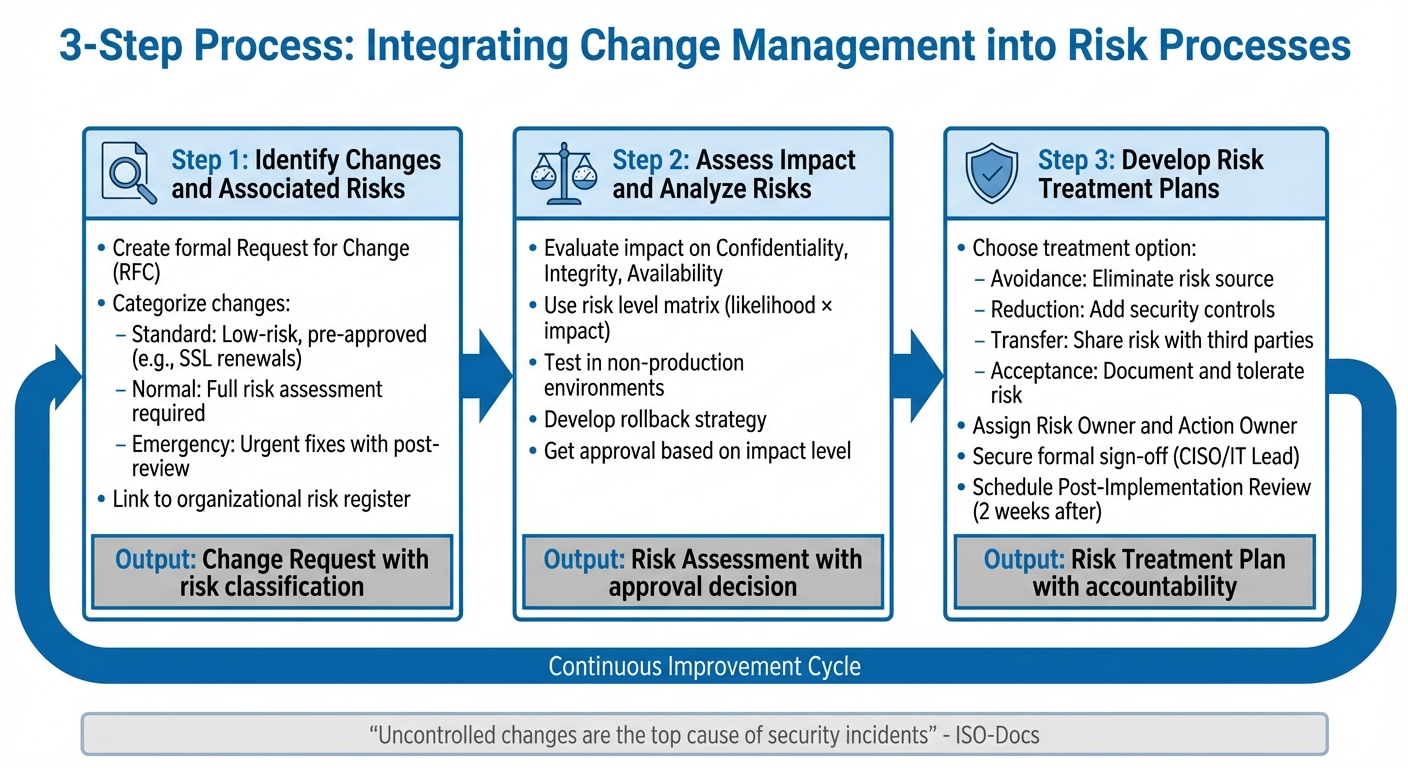
ISO 27001 Change Management and Risk Integration 3-Step Process
Building on the principles of ISO 27001's planning and operational controls, this section lays out a straightforward process to integrate change and risk management. By aligning these two areas, you can create a workflow that anticipates security challenges and ensures every change aligns with your ISMS's core security objectives. The process involves three key steps to ensure every modification undergoes thorough evaluation.
Step 1: Identify Changes and Associated Risks
Every proposed change begins with a formal Request for Change (RFC), which outlines the modification, its purpose, and the timing. This documentation acts as a safeguard against unplanned changes that might expose vulnerabilities.
Categorize changes to guide the process. Changes fall into one of three categories:
- Standard: Routine, low-risk tasks like SSL certificate renewals that are pre-approved.
- Normal: Non-routine changes that need a full risk assessment and approval.
- Emergency: Urgent fixes for critical vulnerabilities, handled quickly but still documented.
Each change request should directly link to your organizational risk register, referencing its associated risk ratings and triggering the appropriate review. Tools like Jira or ServiceNow can help centralize this process, capturing details such as the change's purpose, scope, affected systems, and initial risk evaluation in a consistent format.
"Change" should be defined broadly to include both technical updates (like patches or hardware replacements) and non-technical shifts (such as changes in roles or office locations). Under Annex A.8.32 of ISO 27001:2022, organizations must formalize their processes to ensure all changes are assessed and approved. Auditors will expect to see a clear audit trail linking the original change request to its risk assessment.
| Phase | Action Item | Description |
|---|---|---|
| Initiation | Change Request | Document the purpose and timing of the proposed change. |
| Classification | Categorization | Assign a risk level (Standard, Normal, Emergency). |
| Identification | Impact Scope | List all systems, data sets, and personnel affected. |
| Risk Linkage | Register Mapping | Connect the change to entries in the ISMS Risk Register. |
Once changes are classified and linked to the risk register, evaluate the potential impact of each one.
Step 2: Assess Impact and Analyze Risks
Evaluate the effect of changes on Confidentiality, Integrity, and Availability to determine whether additional controls are necessary. This step helps decide if the risk is acceptable or if further measures are required.
A risk level matrix can quantify the stakes. For instance:
- A change with high likelihood and high impact would be flagged as "Critical."
- Low likelihood and low impact would fall under "Low."
This scoring method simplifies decision-making by providing a clear picture of the risks. As ISO-Docs highlights:
Uncontrolled changes are the top cause of security incidents. A formal policy ensures every change is assessed, approved, and tested before it's rolled out.
Testing in controlled environments is critical for Normal and Emergency changes. These modifications should be validated in sandbox or non-production environments to detect potential security gaps or compatibility issues. Every change plan must also include a rollback strategy to restore the system if the implementation fails or causes unforeseen problems.
An approval matrix can streamline this process:
- High-impact changes require sign-off from senior leadership or a Change Advisory Board (CAB).
- Minor changes follow a simpler workflow.
This tiered system balances thorough oversight with operational efficiency.
Step 3: Develop Risk Treatment Plans for Changes
After assessing the risks, create a Risk Treatment Plan (RTP) to address any vulnerabilities introduced by the change. ISO 27001 offers four treatment options:
- Avoidance: Remove the risky activity altogether.
- Reduction: Apply controls like encryption or multi-factor authentication.
- Transfer: Shift the risk to a third party, such as through insurance or outsourcing.
- Acceptance: Document and accept minor risks when mitigation isn't cost-effective.
Assign clear roles to ensure accountability:
- A Risk Owner monitors the risks.
- An Action Owner implements the necessary controls.
| Treatment Strategy | Action Taken | Example in Change Management |
|---|---|---|
| Avoidance | Eliminate the risk source | Discontinuing a project with unacceptable security risks. |
| Reduction | Add security controls | Enabling multi-factor authentication on new systems. |
| Transfer | Share the risk with third parties | Purchasing cyber insurance or outsourcing high-risk tasks. |
| Acceptance | Tolerate the risk | Choosing to live with a minor vulnerability. |
Before implementation, secure formal sign-off from an authorized stakeholder, such as the CISO or IT Lead. As Sprinto points out:
If it isn't documented, it's as if it never happened.
Keep detailed records of approvals, especially for accepted risks, to demonstrate accountability.
Finally, schedule a Post-Implementation Review (PIR) about two weeks after deployment. This follow-up ensures the change achieved its goals and didn't introduce new security issues. It also provides valuable insights to improve future change management processes.
sbb-itb-b92d866
Best Practices for Change and Risk Integration
Once your organization has established the foundational process for integrating change and risk management, the next challenge is weaving these practices into your daily operations. This ensures your ISMS remains aligned with compliance requirements while staying responsive to new threats. The following strategies focus on embedding oversight and fostering ongoing refinement in your processes.
Establish a Clear Governance Framework
Having a governance framework in place is key to defining roles and responsibilities throughout the change and risk process. Without clear accountability, even the most well-crafted policies can fall apart. A RACI matrix is a great tool to outline who is Responsible, Accountable, Consulted, and Informed for each task. This structure prevents unauthorized changes and ensures significant modifications are reviewed with the appropriate level of scrutiny.
Your governance framework should assign specific roles across teams, reinforcing the earlier steps of risk assessment and approval. Here's an example of how responsibilities might be distributed:
| Role | Responsibility |
|---|---|
| Top Management / Board | Set the organization's risk appetite and allocate resources. |
| CISO / Security Committee | Manage implementation and approve risk treatment strategies. |
| Department Heads | Ensure their teams follow change management policies. |
| Change Advisory Board (CAB) | Review and approve high-impact or high-risk changes. |
Authorization levels should correspond to the impact level of each change. For example, major changes might require sign-off from IT leadership or compliance teams, while routine updates (like SSL certificate renewals) can follow a simpler workflow. Maintaining a "Standard Changes" appendix for low-risk activities can streamline these processes, reducing bottlenecks for the CAB while keeping operations efficient.
Before rolling out changes organization-wide, pilot them within a single department. This allows you to identify and address any issues early on. Additionally, auditors often look for evidence of consistent application, so keep detailed logs of changes, approvals, and meeting minutes to demonstrate compliance.
Use Standardized Processes and Templates
Standardized processes and templates are essential for ensuring consistency across departments. They help unify the language and logic used in risk assessments, bridging any gaps between IT and security teams. For instance, requiring a risk assessment as part of every change request form ensures that no high-impact modification bypasses proper review.
Templates also simplify documentation. By including key elements outlined in Annex A 8.32, such as rollback plans and impact analyses, they make it easier to meet audit requirements. As Nojus Bendoraitis, General Counsel at Copla, explains:
A good template simplifies your initial setup and promotes consistency... It ensures everyone is working from the same risk language and assessment logic.
Linking each change to your risk register and asset inventory can speed up impact analysis and provide a clearer view of how specific modifications affect your overall risk profile. Automated tools can also play a huge role here. For example, implementing automated evidence collection and workflows can cut audit prep time by as much as 80%. Scheduling follow-up tickets in ITSM tools like Jira or ServiceNow two weeks after a change can help you gather data on its success and identify any unforeseen security gaps.
Build a Culture of Continuous Improvement
Formal processes are important, but a culture of continuous improvement ensures your ISMS evolves with new challenges. ISO 27001 Clause 10.1 emphasizes the need for organizations to continually enhance the effectiveness of their ISMS. This isn't just about meeting compliance - it’s about transforming your ISMS into a flexible system that adapts to emerging risks.
The PDCA cycle (Plan-Do-Check-Act) is a great way to structure this approach:
| PDCA Phase | Action for Change & Risk Integration |
|---|---|
| PLAN | Set ISMS goals, identify risks, and create change policies. |
| DO | Implement controls, execute risk treatments, and roll out changes. |
| CHECK | Monitor outcomes, conduct audits, and review change results. |
| ACT | Address root causes, update procedures, and refine the ISMS. |
When issues or failed changes arise, use root cause analysis tools like the "5 Whys" or Fishbone diagrams to address the underlying problem rather than just treating the symptoms. Keep your risk register up to date with lessons learned from recent changes or incidents. Employees at all levels should be encouraged to contribute, as they often spot inefficiencies or risks first.
Lucy Murphy, Head of Customer Success at Hicomply, highlights the value of this approach:
Continuous improvement transforms the ISMS from a compliance exercise into a strategic asset.
Organizations are increasingly embedding change management and risk assessment into everyday tools like Slack, Microsoft Teams, and Jira. This makes continuous improvement a natural part of daily workflows, rather than an afterthought.
Tools to Automate Change and Risk Management
Automating change and risk management simplifies your journey toward ISO 27001 compliance by making documentation and control processes more efficient. Relying on manual spreadsheets or disconnected systems can leave gaps that auditors might flag. Modern tools close these gaps by capturing every change, linking it to your risk register, and producing audit-ready evidence automatically. The right tools integrate seamlessly into your daily workflow - whether you use Slack, Microsoft Teams, Jira, or your CI/CD pipeline - embedding compliance into your routine operations.
Key features to look for include automatic logging of system updates with timestamps, triggering automated risk assessments for every change request, and mapping evidence directly to Annex A controls (e.g., A.8.32). These capabilities can cut audit preparation time by as much as 80%. Real-time monitoring is another must-have; top-tier platforms immediately alert your team if a change compromises security controls, such as encryption or access permissions, helping you avoid compliance issues.
As Bhavyadeep Sinh Rathod, Senior Content Writer at Sprinto, puts it:
The goal isn't to add bureaucracy but to prove that every change is secure, auditable, and aligned with your information security objectives.
When choosing a platform, prioritize those that classify changes by impact - standard, emergency, or major changes - allowing for smoother approvals while maintaining strict oversight of high-risk modifications. Integration with DevOps tools ensures that compliance doesn’t slow down your engineering processes. Automated post-change reviews, like follow-up tickets issued two weeks after implementation, help confirm that changes meet their objectives without introducing new risks.
Below, we’ll look at how tools like ISMS Copilot and ISMS Directory bring these automation features into your workflow.
Using ISMS Copilot for ISO 27001 Compliance
ISMS Copilot is designed to simplify change management within your risk framework by automating key compliance tasks. Unlike general-purpose AI platforms like ChatGPT, ISMS Copilot is specifically trained on ISO 27001 implementation practices, offering tailored guidance based on real-world consultant workflows.
The platform handles tasks like analyzing risk assessments, drafting policies in minutes, and processing lengthy documents (over 20 pages) with ease. It supports the entire PDCA cycle by helping you conduct risk assessments, identify risks, define treatment plans, and justify risk acceptance decisions. For change management, ISMS Copilot assists in creating and refining the policies and procedures required by ISO 27001, ensuring continuous improvement.
ISMS Copilot accelerates compliance work by handling time-consuming tasks like policy writing and document analysis.
Security is a top priority for ISMS Copilot, with no data used for AI training and EU-based data storage in Frankfurt to meet GDPR requirements. Pricing starts at $24/month for the Plus plan (suited for individual consultants), $100/month for the Pro plan (ideal for power users and consultancies), and $250/month for the Business plan (for teams managing multiple projects). A free version is also available for testing.
To get the most out of ISMS Copilot, use specific prompts and reference the correct ISO 27001 version (2013 or 2022) to ensure accurate control mapping. Always anonymize sensitive data before inputting it into the tool, and double-check AI-generated outputs against official ISO documents to catch any potential inaccuracies.
Finding Service Providers via ISMS Directory
If your organization needs external expertise, the ISMS Directory can connect you with qualified ISO 27001 service providers. Available at https://ismsdirectory.com, the platform helps you find compliance platforms, consulting firms, internal and external auditors, training programs, and certification bodies across various regions.
Whether you’re looking for a specialized platform like Fusion (tailored for regulated industries like Fintech and BFSI), consulting services to establish a governance framework, or training to enhance your team’s skills in change and risk management, the directory simplifies the search. It lists vetted providers offering services like multimodular GRC platforms (e.g., GRASP, used by over 14,000 users) or consulting support to pilot changes, build RACI matrices, and prepare for audits.
Using a directory saves time and ensures you’re working with experts who understand the complexities of ISO 27001 compliance. This is particularly helpful when scaling your capabilities - whether by hiring external auditors for a pre-certification review or finding a training provider to educate department heads on change management policies.
Conclusion
Blending change management with risk management isn’t just about ticking off boxes for ISO 27001 compliance - it’s about safeguarding your organization from potential security mishaps. Every update, patch, or system tweak comes with risks that could impact the confidentiality, integrity, or availability of your data. Taking a structured approach ensures these risks are evaluated before implementation, instead of scrambling to fix issues after something goes wrong.
Consider this: organizations adopting ISO 27001 have reported a 40% drop in security incidents, and solid risk management practices can slash data breaches by 50% in just a year. On the flip side, Interserve’s $4.4 million fine in 2022 highlights the cost of neglecting robust risk management processes. The difference? A clear, documented trail of decisions - complete with Change Requests, Risk Assessments, Approvals, and Testing records - that shows every change was intentional, authorized, and secure [34,8].
ISO 27001 Lead Auditor Stuart Barker emphasizes:
"Auditors are looking for the Paper Trail of Decisions. They don’t just want to see that you made a change; they want to see the Change Request Form that proves authorization, risk assessment, and success criteria."
Adopting a "Stop and Check" rule before making changes to firewalls, servers, or cloud configurations can help identify whether a proposed modification might compromise security. Segregating duties - ensuring the person requesting a change isn’t the one approving it - and planning rollback strategies are also key steps to maintain secure operations [34,3]. Integrating these practices into everyday workflows, whether through Slack, Microsoft Teams, or CI/CD pipelines, makes compliance a natural part of your processes.
Switching from manual spreadsheets to automated platforms doesn’t just save time - it delivers real-time oversight of changes, prevents compliance drift, and ensures critical security measures like encryption and access controls remain intact [3,8]. When change and risk management operate as a unified system, your Information Security Management System (ISMS) becomes more resilient, auditable, and ready to tackle future challenges.
FAQs
What counts as a “significant change” under ISO 27001?
Under ISO 27001, a "significant change" involves updates to systems, processes, or roles that might affect information security. These changes demand a structured approach, including formal review, approval, testing, and proper documentation, to safeguard confidentiality, integrity, and availability of information. Examples could include rolling out updates to essential software, altering job responsibilities, or implementing new technologies.
How do we tie each change request to the risk register and SoA?
To align each change request with the risk register and the Statement of Applicability (SoA) in ISO 27001, start by evaluating the change for any potential security risks. Document these identified risks in the risk register to ensure they are tracked and managed effectively. Once a change is approved, link it to the appropriate controls listed in the SoA. This ensures clear traceability and helps maintain compliance by integrating risk management with the Information Security Management System (ISMS). It also ensures that controls are updated to address any new or modified risks.
What evidence will an auditor expect for emergency changes?
Auditors usually look for documented evidence when reviewing emergency changes. This includes items like approved change request logs, records of impact assessments, testing and validation documentation, and sign-off records. These documents help ensure that emergency changes are handled responsibly and comply with ISO 27001 standards, showcasing proper management and control.