Internal vs External Audits: What's the Difference?
Internal and external audits are both critical for achieving ISO 27001 certification, but they serve different purposes. Internal audits are conducted by your team or hired consultants to identify and address gaps in your Information Security Management System (ISMS). They act as a preparatory measure, ensuring your security practices align with ISO 27001 standards before an external review. External audits, performed by accredited Certification Bodies, provide an independent evaluation to confirm compliance and grant certification.
Key Takeaways:
- Internal Audits: Focus on finding and fixing gaps, improving processes, and preparing for certification. Conducted by internal staff or consultants.
- External Audits: Independent assessments by third-party organizations to certify compliance with ISO 27001. Required for official certification.
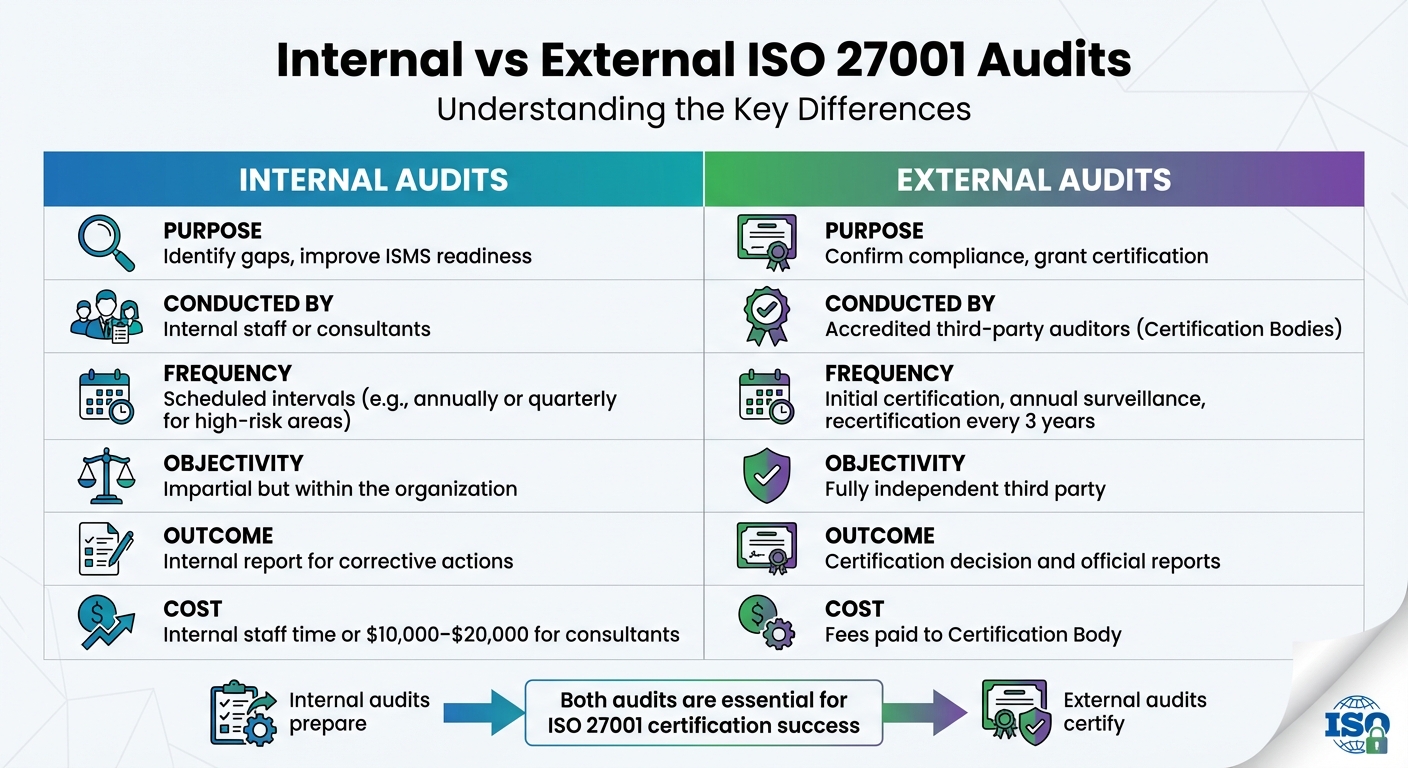
Quick Comparison:
| Aspect | Internal Audit | External Audit |
|---|---|---|
| Purpose | Identify gaps, improve ISMS readiness | Confirm compliance, grant certification |
| Frequency | Scheduled intervals (e.g., annually) | Initial certification, annual surveillance, recertification every 3 years |
| Conducted By | Internal staff or consultants | Accredited third-party auditors |
| Outcome | Internal report for corrective actions | Certification decision |
| Cost | $10,000–$20,000 for consultants | Fees paid to Certification Body |
By combining both audits effectively, you can ensure your ISMS meets ISO 27001 requirements while minimizing risks and costs.
Internal vs External ISO 27001 Audits: Key Differences Comparison
ISO 27001 Internal Audit Essentials: Everything You Need to Know
What Are Internal Audits in ISO 27001?
An ISO 27001 internal audit is a structured, independent review of your organization's Information Security Management System (ISMS). The purpose is to ensure your security practices align with ISO 27001 standards and your internal policies. Think of it as a routine check-up for your ISMS to verify that everything is functioning as it should.
Clause 9.2 of ISO 27001 mandates these audits, requiring them to be conducted at planned intervals. This isn’t just about ticking boxes for certification - it’s about spotting gaps or weaknesses before external auditors do. Internal audits also help fine-tune your security measures and improve overall practices.
Purpose and Scope of Internal Audits
Internal audits are designed to confirm that your documented security policies are actually being followed day-to-day. They also evaluate whether your security controls effectively manage risks. The audit should cover all parts of your IT environment, from cloud systems to third-party services that interact with your ISMS.
One of the biggest advantages of internal audits is catching issues early. Whether it’s a control failure, inefficiency, or compliance problem, identifying these early means they can be fixed more easily and cost-effectively before a formal certification audit. Findings from these audits are categorized as:
- Major Non-conformities: Indicating systemic problems.
- Minor Non-conformities: Highlighting isolated issues.
- Observations: Suggesting areas for improvement.
As Marsel Fazilov, GRC Security Program Manager at Vanta, explains:
"The risk assessment can also provide insight into controls that internal auditors assess as part of a risk-based auditing approach. Specifically, auditors can assess controls mapped to risks with higher scores instead of assessing random control areas."
It’s recommended to conduct a full ISMS internal audit at least once a year. However, high-risk areas may require more frequent reviews.
Who Conducts Internal Audits?
Internal audits can be carried out by your own staff or by external consultants. The key is maintaining objectivity - auditors shouldn’t evaluate their own work or review controls they helped set up. ISO 27001 Clause 7.2 requires that auditors be competent, which means having the right education, training, or experience, along with a solid grasp of auditing and ISO 27001 standards.
Christina Chabot-Olson, Senior Manager of Product Solutions at AuditBoard, highlights:
"The key requirement in the selection of an internal auditor is independence, meaning the internal auditor should be independent of the function being audited."
If your team lacks the necessary expertise or independence, outsourcing the audit is a common solution. External firms typically charge between $10,000 and $20,000 for this service.
Once independence and expertise are confirmed, the audit process can proceed in a structured manner.
Key Steps in an Internal Audit
Internal audits follow a clear, step-by-step process:
- Scope Definition and Documentation Review: Start by defining the audit’s scope and reviewing critical documents like the ISMS Scope Statement, Statement of Applicability, and Risk Treatment Plan.
- Fieldwork and Testing: This involves interviews, walkthroughs, and gathering evidence (e.g., system logs, screenshots) to confirm that daily operations align with documented policies. Sampling is often used to review a representative set of records.
- Analysis and Reporting: Findings are documented, categorized by severity, and analyzed to uncover root causes of any issues.
- Follow-up: Corrective actions are implemented to address the findings and prepare for the external audit.
What Are External Audits in ISO 27001?
An external audit is an independent evaluation carried out by an accredited Certification Body (CB) to confirm that your Information Security Management System (ISMS) complies with ISO 27001 standards. Unlike internal audits, which are under your control, external audits are the only way to achieve an official ISO 27001 certification. This certification signals to customers, partners, and stakeholders that your organization has implemented strong information security practices.
As ISOQAR puts it:
"All audits are based on the same principle of checking that you are actually doing what you say you are doing in your documented Management System and verifying that it's compliant with the ISO standard."
Once certified, the certification is valid for three years, with annual surveillance audits ensuring your compliance remains intact.
Purpose and Scope of External Audits
The main objective of an external audit is to independently confirm that your ISMS meets ISO 27001 requirements. It ensures that your documented security controls and processes are not only in place but also effective at managing risks.
External audits follow a three-year certification cycle. After the initial certification audit, your organization will undergo surveillance audits in the first two years. In the third year, a recertification audit is conducted to renew the certification.
Christina Chabot-Olson, Senior Manager of Product Solutions at AuditBoard, explains:
"ISO 27001 certification provides assurance to stakeholders, customers, and partners that the organization has implemented robust information security measures, potentially enhancing trust and credibility."
Who Conducts External Audits?
External audits are carried out by independent Certification Bodies, often referred to as registrars. These third-party organizations are accredited by national accreditation bodies. For instance, in the U.S., the ANSI National Accreditation Board (ANAB) oversees the accreditation of 38 ISO/IEC 27001 certification bodies. Similarly, the United Kingdom Accreditation Service (UKAS) serves this role in the UK.
It's important to note that ISO itself does not issue certifications. That responsibility lies solely with these accredited bodies. Before engaging a Certification Body, verify their credentials through the International Accreditation Forum's global database, IAF CertSearch.
Key Phases of an External Audit
External audits are conducted in two main stages:
- Stage 1 (Documentation Review): This is a readiness assessment, typically lasting 1–2 days for small to medium-sized businesses. During this stage, the auditor reviews your ISMS documentation - such as scope, policies, risk assessments, and the Statement of Applicability - to ensure you’re prepared for the full audit. This phase can often be completed remotely or at your main office. Any gaps identified are documented as "Improvement Requests", which must be addressed before moving on to Stage 2.
Evan Rowse, a GRC Subject Matter Expert at Vanta, explains:
"Stage 1 ISO 27001 audit resembles a review of your business plan with an external auditor... Stage 2 verifies that your documented plans are effectively implemented."
- Stage 2 (Certification Audit): This phase focuses on verifying that your ISMS is both implemented and effective. It involves on-site visits, interviews, and control testing to confirm that your security measures are functioning as intended. Depending on the size and complexity of your ISMS, this stage can last anywhere from 2 to over 12 days. The auditor will either recommend certification or identify nonconformities that must be addressed. Major nonconformities typically need to be resolved within 90 days for certification to proceed.
Organizations must complete both stages within six months to avoid repeating Stage 1. For small- to mid-sized businesses, the entire certification process generally takes 6 to 12 months. Larger organizations with more complex ISMS scopes may need up to 18 months to complete the process.
These structured steps guide your organization from preparation to certification, ensuring readiness and compliance.
Internal vs External Audits: Key Differences
This section highlights the differences between internal and external audits, helping you fine-tune your certification strategy. While both types evaluate your Information Security Management System (ISMS), they serve distinct roles and operate under unique conditions. Grasping these differences can guide you in allocating resources efficiently and preparing effectively for each audit.
Internal audits focus on identifying gaps and driving continuous improvement. These are carried out by your team or external consultants you hire, with findings kept within your organization. They are typically scheduled at planned intervals, such as annually or quarterly for high-priority areas.
External audits, on the other hand, are formal evaluations conducted by accredited Certification Bodies. These audits determine whether your organization meets ISO 27001 requirements and are part of a strict three-year certification cycle. This includes an initial certification audit, annual surveillance audits for the first two years, and a recertification audit in the third year.
The level of objectivity is another key difference. Internal auditors must be impartial and not audit their own work, but they are still part of your organization. External auditors, however, are completely independent third parties, offering unbiased evaluations that reassure customers, partners, and regulators.
Here’s a quick side-by-side comparison of the two types:
Comparison Table: Internal vs External Audits
| Aspect | Internal Audit | External Audit |
|---|---|---|
| Purpose | Identify gaps, improve ISMS readiness | Assess compliance, grant/maintain certification |
| Frequency | Scheduled intervals, e.g., annually or quarterly | Initial certification, annual surveillance, recertification every 3 years |
| Cost | Internal staff time or $10,000–$20,000 for consultants | Fees paid to a Certification Body |
| Expertise | Internal staff (independent of the area) or consultants | Accredited third-party auditors |
| Objectivity | Impartial but within the organization | Fully independent third party |
| Outcomes | Internal report for corrective actions | Certification decision and official reports |
Understanding these distinctions ensures you're well-prepared for both internal evaluations and external certifications, setting your ISMS up for success.
sbb-itb-b92d866
Internal Audits: Benefits and Challenges
Benefits of Internal Audits
Internal audits play a central role in refining and improving an organization's Information Security Management System (ISMS), especially under the ISO 27001 framework. Their importance lies in their ability to identify issues early, allowing organizations to address compliance gaps, missing controls, or ineffective security measures before they escalate. This proactive approach can prevent costly consequences, considering that the global average cost of a data breach in 2024 has reached approximately $4.88 million.
Another advantage is how internal audits encourage ongoing improvement. They highlight areas for both minor tweaks and larger-scale enhancements, helping organizations adopt best practices across various departments. A risk-based approach ensures that resources are directed toward high-risk controls, maximizing the effectiveness of the audit process.
Internal audits also offer scheduling flexibility. Unlike external audits, which follow strict timelines, internal audits can be conducted monthly or quarterly, reducing pressure on teams. This flexibility allows organizations to manage the timing, scope, and depth of their reviews. Additionally, automation tools can streamline these processes, cutting manual effort - like evidence collection - by up to 80%, making audits less burdensome for staff.
Finally, internal audits provide a solid foundation for justifying security investments. By documenting inefficiencies or gaps, they help build a compelling case for securing budget approvals for training, new hires, or technology upgrades. This documentation can be instrumental in gaining management support.
Challenges of Internal Audits
While internal audits bring many benefits, they also come with challenges that organizations must navigate.
One of the biggest hurdles is ensuring auditor independence. ISO 27001 requires that auditors remain impartial and avoid auditing their own work or processes they implemented. This can be tricky for smaller organizations, where employees often juggle multiple roles. As Daniel Djiann, Head of ISO & Business Continuity Practice at Evalian, explains:
"An audit report produced by a specialist organisation may carry more weight and be more readily accepted if coming from outside of the organisation and away from internal politics".
Another challenge is the lack of expertise. Small businesses and startups may not have staff with the necessary training or experience to perform a thorough ISO 27001 audit. While the standard doesn’t require specific certifications, Clause 7.2 emphasizes that auditors must be competent through education, training, or experience. For organizations lacking internal expertise, hiring third-party specialists is an option, but it comes at a cost - typically ranging from $10,000 to $20,000. For those on tight budgets, this can be a significant expense.
Lastly, audit fatigue can impact productivity. When audits are added to employees' regular tasks, it can overwhelm teams, particularly in security and other departments. Manual processes, such as managing scattered spreadsheets and outdated documents, further complicate evidence collection, increasing inefficiencies and the likelihood of errors. On average, internal audits take one to three weeks to complete, often leading to noticeable drops in productivity within the audited areas during that time.
External Audits: Benefits and Challenges
Benefits of External Audits
External audits offer an unbiased, third-party review that's essential for ISO 27001 certification. When conducted by reputable accreditation bodies like UKAS or ANAB, this objectivity becomes a cornerstone of the certification process. As Evan Rowse, GRC Subject Matter Expert at Vanta, explains:
"The stages of the audits can be best seen as proving that security is built into the business, not just bolted on."
This level of scrutiny doesn’t just meet certification standards - it also builds credibility with customers. By demonstrating strong security practices, businesses can gain a competitive edge and even shorten their sales cycles. This is especially crucial in the U.S., where the average data breach cost hit $9.44 million in 2022 - a staggering $5.09 million higher than the global average. External auditors also bring fresh perspectives, often identifying vulnerabilities that internal teams might overlook, reducing the risk of costly incidents.
The certification process itself encourages ongoing improvement. Regular surveillance audits and mandatory recertification every three years ensure your ISMS stays aligned with new threats and operational changes. Additionally, external audits help satisfy legal and contractual obligations, as many agreements now require ISO 27001 compliance backed by third-party validation.
While the benefits are clear, the process comes with its own set of challenges.
Challenges of External Audits
Meeting external audit standards can be a demanding task. These audits require significant time, effort, and resources, which can put compliance teams under considerable pressure. The formal nature of the process means that any major nonconformities - serious flaws in your ISMS - could block certification entirely. The Cloud Security Alliance highlights this risk:
"A single major non-conformity will prevent an organization from obtaining or maintaining the ISO 27001 certification."
One common hurdle is documentation. Relying on manual processes or scattered spreadsheets can make it hard to provide evidence quickly during an audit. For small-to-medium businesses, the certification process can take 6–12 months, while larger organizations may need up to 18 months. Adding to the complexity, Stage 1 and Stage 2 audits must occur within six months of each other - otherwise, the entire Stage 1 process must be repeated.
Costs are another challenge. External audits can run into tens of thousands of dollars, depending on the size and complexity of your organization. For smaller businesses and startups, the lack of internal expertise can make the process even more daunting. There’s also the risk of auditor overreach, where auditors might suggest specific controls or technologies. As Justin Beals, Founder & CEO of Strike Graph, points out:
"Auditors should not necessarily be seen as your security officers or even analysts... who owns the design of your security practice? ... It's that organization."
To overcome these challenges, preparation is key. Conduct internal readiness reviews well before the external audit, use automation tools to streamline evidence collection (potentially cutting prep time by nearly 50%), and be upfront about any known gaps. Auditors value accountability over superficial compliance. By taking these steps, organizations can navigate the audit process more effectively and with greater confidence.
How to Combine Internal and External Audits for ISO 27001 Success
Using Internal Audits to Prepare for External Audits
Internal audits are like a health check for your Information Security Management System (ISMS), helping you spot and fix control gaps before they become bigger issues. ISO 27001 Clause 9.2 makes these audits mandatory, so skipping or treating them casually could lead to major compliance problems. As Radhika Sarraf, Content Marketer at Sprinto, puts it:
"Internal audits are not optional. ISO 27001 Clause 9.2 clearly requires you to plan, conduct, and maintain internal audits at defined intervals."
To make your internal audits effective, divide them into two parts: a documentation review and practical testing. This ensures your policies aren’t just words on paper but are actually being implemented. Focus on high-risk areas like access management and incident response, and consider reviewing these areas quarterly for added assurance. When you find gaps, dig into the root cause, assign corrective actions, and set clear deadlines for resolution. Keep detailed records of major non-conformities and address them before your external audit.
Most organizations spend about one to three weeks preparing for an external audit. This effort not only smooths the path for external evaluation but also strengthens your ISMS, making it more resilient in the long run.
Finding Audit Services Through ISMS Directory
Once your internal processes are in good shape, the next step is finding the right audit providers. Selecting qualified internal and external auditors is crucial for ISO 27001 certification. The ISMS Directory is a helpful resource, offering a centralized platform to connect with certified internal auditors and accredited certification bodies across various regions. Through this platform, you can find experienced specialists who provide objective and impartial audit services.
If your internal team lacks the expertise or independence required (since auditors shouldn’t evaluate their own work), hiring an independent specialist through the ISMS Directory is a smart move. The platform can connect you with professionals who bring both expertise and neutrality to the table. Plus, its AI assistant can help you find audit services tailored to your industry - whether you need support for internal audits, consulting, or certified third-party reviews. This streamlined process ensures a smooth transition from internal preparation to formal external certification. By working with experts who understand both the technical and practical aspects of maintaining an effective ISMS, you’ll be better equipped to achieve ISO 27001 certification.
Conclusion
Grasping the distinction between internal and external audits is key for any organization aiming for ISO 27001 certification. Internal audits help pinpoint gaps and evaluate controls to ensure your ISMS aligns with documented standards. On the other hand, external audits, carried out by accredited Certification Bodies, provide the independent verification required for ISO 27001 certification. While both types of audits are necessary, only external audits can grant official certification.
By combining these audits, you can identify and address non-conformities early, minimizing obstacles during certification. Treat internal audits as a readiness check, and use a thorough root cause analysis to tackle findings effectively. This approach boosts confidence when facing external audits.
ISO 27001 certification follows a three-year cycle, with annual surveillance audits to confirm your ISMS remains effective. This ongoing process not only ensures compliance but also reinforces stakeholder confidence in your organization's security measures.
As Mark Sharron, Search & Generative AI Strategy Lead at ISMS.online, explains:
"Without verifying how your ISMS is managed and performs, there is no real guarantee of assurance that it is delivering against the objectives it is set to fulfil. Audits go some way to providing this assurance."
To simplify your certification journey, consider utilizing the services available through ISMS Directory. Whether you're looking for qualified internal auditors, consulting support, or accredited certification bodies, ISMS Directory serves as a one-stop platform tailored to your industry and region. Additionally, their AI assistant, ISMS Copilot, connects you with experts skilled in both technical and practical aspects of ISMS management. With these tools, you can efficiently transition from internal preparation to formal certification, ensuring your organization remains secure and certified.
FAQs
How do internal audits support preparation for ISO 27001 certification?
Internal audits are key to getting ready for ISO 27001 certification. They help spot nonconformities and pinpoint ways to improve your Information Security Management System (ISMS). Essentially, these audits ensure your organization aligns with ISO 27001 requirements and is set for the external certification process.
By running internal audits regularly, you can tackle potential problems early, refine your processes, and enhance your overall approach to information security. This doesn’t just prepare you for certification - it also helps maintain compliance over time and strengthens your defenses against security threats.
What challenges do organizations commonly face during ISO 27001 external audits?
Organizations often encounter hurdles when undergoing ISO 27001 external audits. A primary challenge lies in achieving full compliance with the standard’s detailed requirements. This means not only implementing the necessary policies and controls but also meticulously documenting every process. Preparing for the audit often demands a significant investment of time and resources, as internal reviews are essential to spot and fix any gaps before the external assessment.
Another issue is the potential disruption to daily operations. External auditors may require access to sensitive data and key personnel, which can temporarily interrupt regular workflows. For organizations with complex systems or teams spread across multiple locations, maintaining consistent security practices and keeping documentation current adds another layer of difficulty.
The best way to navigate these challenges? Focus on thorough preparation. Regular internal audits, coupled with well-organized and up-to-date documentation, can go a long way in ensuring the external audit process runs smoothly.
Why is it important for internal auditors to remain independent, and how can this be achieved?
Keeping auditors independent during internal audits is essential for delivering an honest and impartial review of your organization's Information Security Management System (ISMS). This impartiality ensures that any weaknesses or areas for improvement are identified without bias or conflicts of interest, preserving the audit's credibility.
To maintain this independence, it's important that internal audits are carried out by individuals who aren't directly involved in the processes being audited. Another effective option is hiring third-party professionals to handle the audit. This external perspective not only ensures neutrality but also reinforces trust in the process, helping your organization stay aligned with ISO 27001 compliance requirements.