ISO 27001 Audit Questions: What Auditors Ask
When preparing for an ISO 27001 audit, knowing what auditors focus on can save you time and prevent errors. These audits assess your Information Security Management System (ISMS) to ensure it aligns with international standards. Auditors evaluate your organization's security practices, documentation, and team awareness to identify gaps and confirm compliance.
Key areas of focus include:
- Context of the Organization: Auditors check if you've identified internal and external factors affecting security. They’ll ask about your ISMS scope, external threats, and how these connect to your risk assessment.
- Leadership and Commitment: Evidence of management's active role in driving security efforts is critical. Expect questions about leadership's involvement in planning, budgeting, and communicating security priorities.
- Risk Assessment and Treatment: Auditors examine how risks are identified, evaluated, and addressed. Be ready to show your risk register, treatment plans, and how controls are applied.
- Planning and Objectives: Your security goals should align with organizational risks and be measurable. Auditors will ask about objectives, metrics, and how these are communicated.
- Support and Resources: Auditors look at resource allocation and staff competence. Training records, policy acknowledgment logs, and evidence of communication processes are commonly reviewed.
- Operation and Implementation: Auditors verify that controls are functioning as intended. Incident logs, operational procedures, and change management records are essential.
- Performance Evaluation: Internal audits, management reviews, and up-to-date risk registers demonstrate ongoing ISMS effectiveness.
- Improvement and Corrective Actions: Auditors expect documented evidence of how non-conformities are addressed and improvements are made.
Annex A Controls: These are grouped into four themes (Organizational, People, Physical, and Technological), and auditors ensure your Statement of Applicability reflects which controls are implemented or excluded, with justifications.
Preparation tips:
- Review your documentation thoroughly.
- Conduct internal audits to identify gaps.
- Train your team to handle auditor interviews confidently.
- Use tools to automate evidence collection and streamline processes.
ISO 27001 certification is no longer optional for many organizations - it’s a way to prove your commitment to security, meet compliance requirements, and build trust with stakeholders.
Top ISO 27001 Audit Interview Questions & Answers
sbb-itb-b92d866
Main Areas Auditors Examine
ISO 27001 auditors follow a structured process, focusing on three core areas of your Information Security Management System (ISMS). These areas are crucial for determining whether your security framework is solid or needs improvement.
Context of the Organization
Auditors begin by assessing how well you understand your internal and external environment. They’ll review documents like SWOT analyses, PESTLE assessments, or strategic plans to ensure you’ve identified the factors impacting your information security. Internal factors could include company culture, resource limitations, or your organizational structure, while external ones might cover legal requirements, market trends, or emerging threats.
A key tool auditors use is the "Golden Thread" traceability audit. This method ensures that issues identified in your context analysis (Clause 4.1) connect directly to your Risk Assessment (Clause 6.1) and Statement of Applicability. For instance, if "Ransomware" is flagged as a critical external threat but doesn’t appear in your Risk Register, it raises a red flag. They’ll also check Management Review Minutes to confirm that "Changes in external and internal issues" is a regular agenda item, proving that your context analysis is an active, living document.
"If it isn't written down, it doesn't exist for the auditor." - Stuart Barker, ISO 27001 Lead Auditor
Expect questions like, "What is the scope of your ISMS?" or "How do you identify relevant external issues?" Auditors will also verify your list of interested parties - such as customers, regulators, and partners - and ensure their requirements are properly addressed in your ISMS scope.
Finally, auditors assess whether leadership is setting the right tone and driving strategic security priorities effectively.
Leadership and Commitment
This area highlights whether your organization genuinely prioritizes security or is simply aiming to check a box for certification. Auditors look for evidence that top management actively leads the ISMS by providing resources and integrating security into core processes.
They evaluate leadership engagement over time - not just a burst of activity right before the audit. This includes reviewing board meeting minutes to confirm that information security is a recurring topic, checking budget approvals for security investments, and examining RACI matrices to ensure roles and responsibilities are clearly defined.
"If the CEO cannot articulate the security policy, the audit ends there." - ISO27001.com
A lack of visible commitment from top management is considered a Major Non-Conformance. Auditors may ask, "How does top management demonstrate commitment to the ISMS?" or "What roles and responsibilities are defined for ISMS management?" They’ll also interview employees to see if leadership’s security priorities have filtered down to staff.
Once leadership involvement is established, auditors shift their focus to your risk assessment and treatment processes.
Risk Assessment and Treatment
This part examines how effectively you identify, evaluate, and address information security risks. Auditors review your risk assessment methodology to ensure it’s consistently applied and documented. They’ll confirm that risks identified in your context analysis are included in your Risk Register and paired with appropriate treatment actions.
Auditors will scrutinize your risk assessment (Clause 8.2) and Risk Treatment (Clause 8.3) to ensure the process is actionable and directly influences your security decisions. They’ll ask questions like, "What methodology do you use for risk assessment?" or "Can you provide evidence of your risk treatment process?" Be prepared to show documentation that reflects quarterly reviews of your risk register, capturing changes in systems, incidents, or organizational shifts.
They’ll also verify that your Statement of Applicability accurately represents which Annex A controls you’ve implemented and why certain controls were excluded. Auditors pay close attention to how you’ve aligned your controls with the updated structure. Expect to explain your methods and present supporting evidence during interviews.
Typical Questions by ISO 27001 Clauses
Auditors take a structured approach when assessing your Information Security Management System (ISMS). They ask specific questions tied to ISO 27001 clauses, so knowing these in advance can help you prepare evidence and avoid unexpected issues during the audit.
Planning and Objectives
Auditors will check that your planning aligns with your risk assessment and organizational goals. Expect questions like, "What are your current information security objectives, and how are they communicated?" or "What metrics are used to track their progress?" To meet expectations, ensure your objectives are measurable - like aiming to "reduce phishing incidents by 20% within six months."
Auditors also rely on the "Golden Thread" concept, tracing a high-priority issue from your context analysis through your Risk Register to the Statement of Applicability (SoA). For instance, if GDPR compliance is mentioned in your context but isn't tied to specific risks or controls, it could result in a non-conformity. Questions might include, "How are risk owners assigned?" and "Is there formal documentation of management's acceptance of residual risks?" Each risk must have a designated owner responsible for its treatment.
"The SoA is often called the 'single most important document' in the ISMS." - SecPortal
If you've marked an Annex A control as "Not Applicable", auditors will expect a detailed justification linked to your risk assessment. They'll also check that your Risk Treatment Plan directly ties to the SoA, showing that selected controls address specific risks.
Finally, they'll evaluate whether the resources and competencies you've documented are sufficient to meet your objectives.
Support and Resources
Auditors will assess whether you've allocated appropriate resources - such as budget, personnel, and technology - and whether your team is qualified for their roles. Questions might include, "What resources are allocated to support the ISMS?" and "How do you ensure personnel are competent in their ISMS responsibilities?" Evidence like training certificates, performance reviews, or employee interviews will be used to verify competence. Employees may be asked to explain the information security policy or describe their specific responsibilities.
Another focus area is documentation control. Auditors will check whether your policies and procedures are version-controlled and securely stored. They'll also ask about your internal and external communication processes - what is communicated, when, to whom, and how. A RACI Matrix that clearly defines roles and responsibilities can help demonstrate compliance. Centralized training records showing participation in security awareness programs are also valuable evidence.
Once planning and support are confirmed, auditors will evaluate how well these measures are applied in daily operations.
Operation and Implementation
Auditors will look at how effectively your security controls are implemented in practice. Questions might include, "How do you ensure controls are implemented effectively?" and "What is your process for managing incidents?" They’ll expect to see evidence such as incident logs, change management records, and operational procedures.
For example, if you use cloud services, you’ll need to show that your controls are actively managed. Auditors will also ensure that the resources identified in Clause 7 align with the risks identified in Clause 6, checking for consistency throughout your ISMS.
Performance Evaluation
Auditors will then assess how you monitor, measure, and review your ISMS performance. Questions could include, "How do you track ISMS performance?" and "What is your process for conducting internal audits?" Evidence might include an internal audit program with detailed plans, schedules, and reports.
"The key requirement in the selection of an internal auditor is independence, meaning the internal auditor should be independent of the function being audited." - Christina Chabot-Olson, Senior Manager of Product Solutions, AuditBoard
Management review meetings are another critical area. Auditors will look for evidence - like meeting minutes - showing that mandatory topics such as audit results, incident trends, resource needs, and ISMS changes were discussed. They'll also check whether your risk register is up-to-date. If it hasn’t been reviewed recently or doesn’t reflect changes like cloud migrations or security incidents, it could result in a non-conformity. Regular updates, such as quarterly reviews, show that your risk register is an active, relevant tool.
Improvement and Corrective Actions
Maintaining certification means showing a commitment to ongoing improvement. Auditors will ask, "What steps have you taken to improve the ISMS?" and "How do you address corrective actions?" A centralized corrective action log is key, tracking the issue, remediation steps, deadlines, and closure for each non-conformity.
"The organization shall retain documented information as evidence of the nature of corrective actions and the results of corrective actions." - ISO 27001 Clause 10.1
Findings are classified as Major or Minor non-conformities. A Major non-conformity - like a complete failure of your access control system - must be resolved before certification. A Minor non-conformity - such as a single lapse in following a procedure - requires a corrective action plan with a set deadline. Auditors will also check that past findings have been addressed and that updates to your ISMS result in meaningful security improvements, not just updated paperwork.
Annex A Control Domains: Auditor Questions
ISO 27001 Annex A Control Domains: Auditor Questions and Evidence Requirements
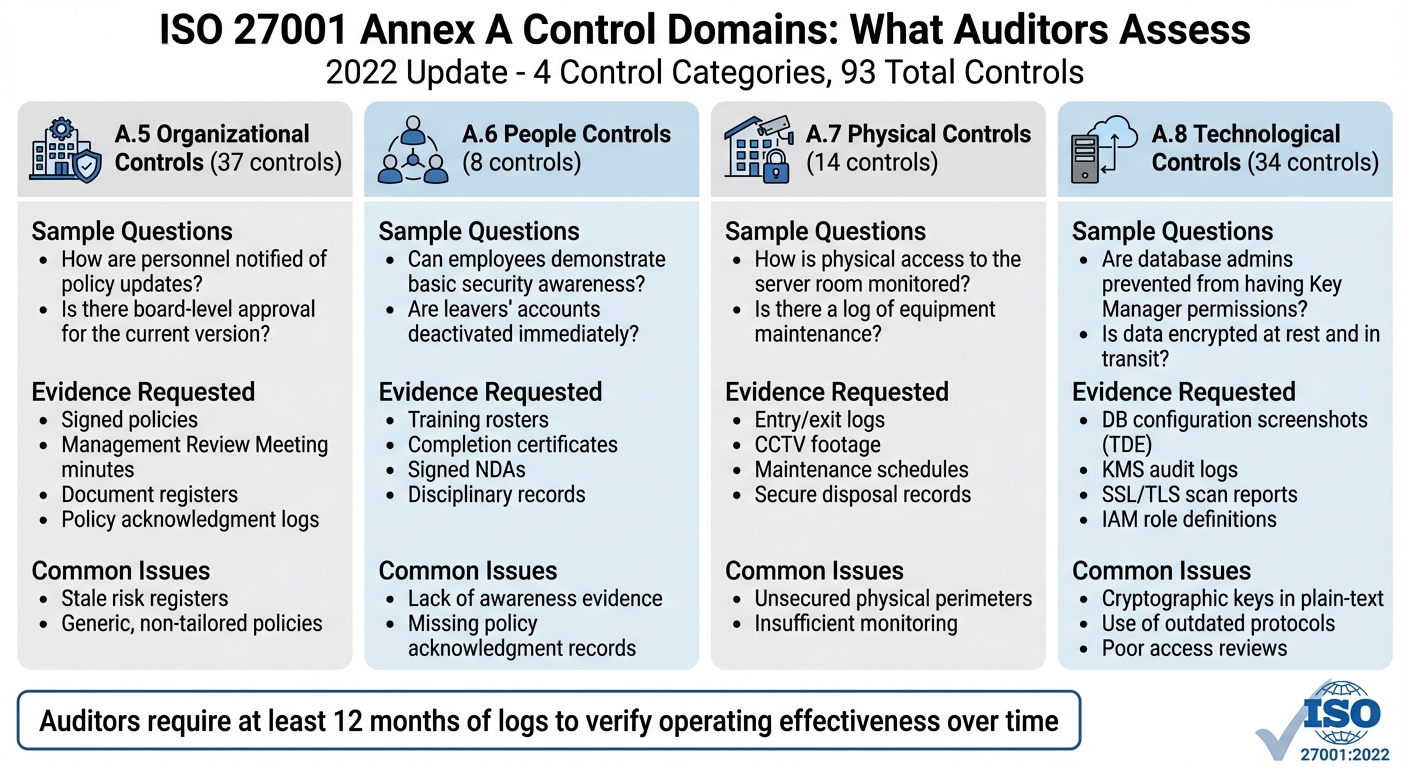
When diving into auditor expectations for Annex A control domains, it's essential to understand how these controls are structured and assessed. The 2022 update to ISO 27001 reorganized Annex A into four themes: Organizational (37 controls), People (8 controls), Physical (14 controls), and Technological (34 controls). Auditors will check that your Statement of Applicability covers all these controls, and any exclusions must be clearly justified based on your risk assessment.
Auditors typically look for three types of proof: Documentation (how the control is designed), Records (logs or reports that show implementation), and Evidence (proof that the control works as intended). A frequent pitfall is relying only on policies without operational proof to back them up.
"A policy is words; a 'Pass' requires proof that 100% of S3 buckets/SQL disks are actually encrypted." - Stuart Barker, ISO 27001 Lead Auditor
Auditors also expect at least 12 months of logs to verify "operating effectiveness" over time, not just a single snapshot. For instance, if you claim quarterly access reviews, you'll need to provide four sets of records from the past year. Automating evidence collection using tools like security platforms, identity management systems, or SIEMs can make this process far smoother.
Annex A Controls Comparison
Here’s a breakdown of how auditors typically evaluate each control category:
| Control Category | Sample Auditor Questions | Typical Evidence Requested | Frequent Nonconformity Types |
|---|---|---|---|
| A.5 Organizational Controls | How are personnel notified of policy updates? Is there board-level approval for the current version? | Signed policies, Management Review Meeting minutes, document registers, policy acknowledgment logs | Stale risk registers; generic, non-tailored policies |
| A.6 People Controls | Can employees demonstrate basic security awareness? Are leavers' accounts deactivated immediately? | Training rosters, completion certificates, signed NDAs, disciplinary records | Lack of awareness evidence; missing policy acknowledgment records |
| A.7 Physical Controls | How is physical access to the server room monitored? Is there a log of equipment maintenance? | Entry/exit logs, CCTV footage, maintenance schedules, secure disposal records | Unsecured physical perimeters; insufficient monitoring |
| A.8 Technological Controls | Are database admins prevented from having Key Manager permissions? Is data encrypted at rest and in transit? | DB configuration screenshots (TDE), KMS audit logs, SSL/TLS scan reports, IAM role definitions | Cryptographic keys in plain-text; use of outdated protocols; poor access reviews |
This table highlights how auditors approach each control domain and the types of evidence they expect. For example, compliance with A.5.1 (policy acknowledgment) often comes down to whether more than 10% of sampled personnel lack proof of acknowledgment within the past year. Similarly, technological controls are scrutinized for issues like "Shadow Admin" privileges, where a Global Admin bypasses separation of duties by having access to a Hardware Security Module.
To simplify the audit process and reduce risks, it's crucial to assign clear ownership of evidence. For example, IT operations might manage monitoring logs, while HR oversees training records. This kind of evidence-mapping framework ensures accountability and keeps audits running smoothly.
Key Takeaways
Getting audit-ready boils down to having clear plans, consistent practices, and solid documentation to back it all up. Auditors aren’t expecting perfection on paper - they’re looking for proof that your ISMS (Information Security Management System) works effectively in real life. This means your documented evidence must show that policies are followed, and your Statement of Applicability should be thorough and based on actual risks.
The deadline to transition to ISO 27001:2022 is October 31, 2025. Waiting until the last minute to make updates adds unnecessary risk. Interestingly, 81% of organizations say they are either certified or planning to be certified by 2025, up from 67% in 2024. Automation can make a big difference here, cutting audit preparation time from weeks to just days. Some organizations even report that internal audits now take only 10% of the time they used to.
"The best audit preparation is a well-functioning ISMS that operates throughout the year - not just a last-minute scramble before the auditor arrives." - Saravanan G, Vice President - Cyber Assurance, Glocert
Tools like ISMS Copilot simplify the process by automating evidence collection, breaking down complex requirements into easy-to-follow tasks, and offering real-time dashboards to track audit readiness. This makes it easier to maintain a proactive, year-round approach that strengthens your ISMS.
Lastly, keep in mind that initial audits often result in 2–5 minor nonconformities. To stay ahead, conduct an independent internal audit at least a month before your external assessment. Prepare your team with mock interviews, and treat risk management as an ongoing process that evolves with changes in your organization. With the right strategies and tools, certification becomes a manageable goal rather than an overwhelming hurdle.
FAQs
What evidence should we have ready before the audit?
Before undergoing an ISO 27001 audit, it's crucial to have all your evidence neatly organized to showcase your controls, policies, and processes. This includes documented risk assessments, control implementations, security logs, meeting records, training records, and operational procedures. Keeping these documents well-structured and easy to access not only demonstrates your compliance with ISO 27001 standards but also ensures you're prepared to address any questions the auditor might have.
How do auditors test that our controls actually work?
Auditors evaluate how well your controls work by examining evidence like documented procedures, logs, and operational records. They check whether these controls are consistently applied and deliver the intended security results. This process often involves reviewing documentation, analyzing operational evidence, and performing hands-on tests to ensure the controls effectively reduce risks and function as they should in practical, everyday situations.
What usually causes major vs. minor nonconformities?
Major nonconformities happen when a critical system element is either completely absent or fails in a way that reveals a deeper, systemic problem. In contrast, minor nonconformities stem from isolated instances of non-compliance that don’t suggest widespread issues within the system. These classifications allow auditors to gauge the seriousness of compliance gaps and understand how they might affect the organization’s overall information security management system.

